2026-05-01 15:23:53
The financial industry understands itself to be an arm of the government. We were inducted into this service other-than-willingly through the ordinary operation of law and regulation.
This is uncontroversial and unsurprising to insiders.
A claim which will be more surprising: some regulated financial institutions have delegated authority for account- and transaction-level decisioning to a non-profit.
Another: that non-profit includes a private intelligence agency, which runs covert assets, publishes intelligence estimates, develops target lists, and communicates them to decisionmakers.
Still another: the non-profit organized a coalition of the willing as an outgrowth of its intelligence agency. The willing non-profits, that is. The coalition engaged in a years-long campaign to coerce financial infrastructure and other firms to give them the ability to direct accounts to be closed. The infrastructure built to do this against domestic terrorists was applied to an American politician’s fundraising efforts, and no one seemed to think that was odd.
Last week, the DOJ unsealed an indictment against the organizing non-profit for bank fraud. This was based, in part, on how it paid the intelligence agency’s covert assets.
They likely developed evidence for that indictment using the Bank Secrecy Act (BSA) mandatory reporting regime.
We begin, as always, with the bank fraud.
White collar prosecutions are structurally difficult because they frequently depend on intent. It is difficult to prove intent beyond a reasonable doubt, as it frequently depends on subjective mental states which we cannot directly observe. This problem is discussed in the literature including in book-length treatments.
There exist ways to overcome this difficulty as a prosecutor.
The classic one is waiting for the criminal to violate Stringer Bell’s dictum on the wisdom of taking notes on a criminal conspiracy. You then introduce their notes into evidence. They will frequently contain explicit statements demonstrating mens rea (a legal concept of a “guilty mind”). The register of those statements will be less guilty and more gleeful. Crime is awesome! Wow I sure hope the government never reads this! Because we are committing so much crime right now!
The prosecutorial toolbox has other tricks, too. Rely less on charges which require demonstrating intent. Rely more on what the economics of law field calls bright-line rules. For those crimes, you do not need to demonstrate what emotional valence someone experienced while committing a criminal act. You only need to demonstrate the fact of the act.
Interdicting crime is an iterated game. Responding to our noted inability to manage some forms of crime, legislators have intentionally added some items to the prosecutorial toolbox. Whether one describes them as tools or weapons depends mostly on whether one touches them with the hand or the face.
As Bits about Money has covered frequently previously, the anti-moneylaundering (AML), Know Your Customer (KYC), and related regulatory edifices function in a subtle manner. They do not simply proscribe conduct and rely on perfect enforcement by the financial industry. To achieve the overall objective of stochastically interdicting crime, the regs are designed to force criminals into repeated unpalatable tradeoffs. One is “You can choose making money, or you can choose never interacting with banks, but it is very difficult to choose both.”
We then follow the criminal into the bank. “By the way, lying to a bank is a crime. It doesn’t matter what you think while you’re doing it. It doesn’t matter why you did it. It doesn’t matter if you’re a sinner or a saint. It doesn’t matter if it is a big lie or a little lie. It doesn’t matter if the bank believes you. Lying to a bank is a crime. And everything you say to a bank will be recorded for decades. It will be routinely forwarded directly to law enforcement if the forward-deployed intelligence analysts we force the bank to hire believe there is even a tiny chance law enforcement will find it useful.”
Al Capone infamously went down for the tax evasion because it was easier to prove than the murders. Drug smuggling is sometimes difficult to prove, but the smugglers will want their money in the regulated financial system. The mandatory questionnaire at account opening will ask “Why are you requesting this account?” They will probably not write down “Drug smuggling!”, because a wag who tries doing so will quickly realize this does not successfully result in a bank account. So they will write any other answer. Now they have lied to a bank.
And then, in the ordinary practice of U.S. prosecutors, you will charge them with any crimes you can prove, including the lie itself. And if you are able to demonstrate that it was in fact a lie, which is easier to prove than e.g. rolling up the entire drug smuggling network, you will then make a simple legal request: give us all the money you lied about. That request will be more directed at the banks than the criminal, and the banks will comply, with alacrity.
Sam Bankman-Fried: SBF continues to believe he is innocent. His argument is, effectively, that being the best investor of his generation excuses stealing the principal to invest. That is not a defense in U.S. law, and the indictment charges fundamentally the same conduct (misappropriating money and crypto investors had on deposit at FTX) under a variety of statutory pathways, including 18 USC §1343 (wire fraud), §1344 (bank fraud), and §1956 (money laundering conspiracy).
Let’s focus on the bank fraud. One part of SBF's criminal empire needed banking in the United States. They could not convince a U.S. bank to let them handle FTX customer funds flows. But they wanted to do that. They incorporated North Dimension, a shell entity. Some shells have legitimate business purposes; this one existed only to deceive. North Dimension filled out a due diligence questionnaire. SBF signed it. It said North Dimension traded on its own account and did not handle customer funds.
You need two bits of evidence to convict SBF of bank fraud. The first fits on one page of paper held by one bank. The second is the answer to a single question: “Did at least one dollar of customer funds flow into the North Dimension account?” Thousands of people at dozens of companies, and hundreds of thousands of electronic documents, know the answer to that question and you only need to find one. A single word convicts.
Other charges can stack on the bank fraud. SBF deployed rationalizations about the core fraud counts like a squid deploys ink. Defeating all of them is unnecessary. A money laundering conspiracy requires showing agreement to a) move money that are the proceeds of at least one of a set of “specified unlawful activities” and b) any act to corrupt the integrity of the paper trail about that money movement.
Bank fraud is a specified unlawful activity.
And so you only need one more sentence to get the second charge. Many many sentences will do. Here’s a question to elicit one: “Caroline Ellison, you are a cooperating co-conspirator. During the duration of your conspiracy, while you were the CEO of Alameda Research, did you at any time direct the North Dimension account to move money on behalf of Alameda Research, knowing that by this direction banking records would reflect the money movement to be directed by North Dimension and not by Alameda Research?” A single word convicts.
SBF was, properly and justly, convicted of all of these crimes and more.
He was not the first and he will not be the last. A brief survey for fellow aficionados of this genre:
Dennis Hastert was accused of horrific acts against children but indicted for other crimes. He could not have been successfully prosecuted on the abuse even with a confession, because it was time-barred long before it came to light.
Hastert paid one of his victims to keep him quiet. He was smart enough to make the payment in cash, but the system was smarter sooner, and made a trivial tripwire for attempting to move large amounts of cash out of the regulated banking system: your bank files a currency transaction report (CTR). Apprised of this, he changed his banking patterns to avoid the filing of a CTR. That is called “structuring” and it is a crime under 31 USC §5324(a)(3).
When the FBI asked him about it they used another frequent prosecutorial tool to pick up a freebie. They asked why he had changed his banking practices. He did not say “To structure transactions to avoid the bank filing a CTR when I pick up hush-money.” Instead, he agreed with the agents suggesting that perhaps he distrusted banks and simply wanted to keep hundreds of thousands of dollars of cash on hand. This gave the prosecutors a second charge of lying to federal officials.
In a routine practice, they agreed to dismiss it if he would simply confess to the structuring. The implicit Or Else: “We go to trial, convict you on both, and you get a longer sentence both because the charges stack and because the sentencing formula will mechanically penalize you for this choice.”
Reggie Fowler was the U.S.-based partner of a payment processor which ripped off Tether. It will still be years before we unravel that ouroboros of crime. But that didn’t need to delay the indictment, because he lied to banks that he was doing real estate development. Trivially a lie; his hundreds of millions had bought neither land nor buildings. Our old friend §1344 brought his new bestie §1343 (wire fraud), not because he defrauded Bitfinex/Tether but because he had caused his ill-gotten bank accounts to move money. Every movement is another crime.
George Santos was indicted for a variety of abuses of the public trust. Prosecutions of elected officials are inevitably tricky business, particularly as finding the precise line between crime and politics-as-usual is contentious. (Many people seem to think that line should move radically every, oh, four years.)
Happily, we have bright lines which don’t move, like “don’t steal credit cards” (§1028A). You can convict on that without needing to explain whether it was done with a gun or a political donation portal.
Then you stack on wire fraud again, because we intentionally make it hard to spend directly on oneself from politics-adjacent pools of money, and so you need to move money at least once to enjoy it.
Why do these indictments, and hundreds more, rhyme so much? Why can we employ these charges to such devastating effect against the rich and powerful, even those in positions of public trust, even those with allies who still love them? Because we maintain textbooks of how to make these cases and make them stick.
White collar criminal cases are like any other high-end bespoke services work. One could imagine that the production function is fully artisanal, like something out of a traditional French restaurant.
You, an aspiring lawyer, labor for years under the eye of a terrifying supervisor. He periodically steps behind you, rips a brief from your hands, screams at your incompetence, and you have learned one new thing. After twenty years, you now write your own indictments. They bear his distinctive stamp but your signature. You have added your own spin, which you will pass on to the rising generation, via the traditional mix of hazing and hands-on instruction.
This happens. But in law, as in restaurants, we are allowed to write down recipes and tell people to just follow the steps.
For example, we in the financial industry are obliged to file Suspicious Activity Reports (SARs). These are basically three-ish page memos. Combined with statutory tools such as those discussed above, these memos will giftwrap charges and convictions. They get saved by the Financial Crimes Enforcement Network (FinCEN) for decades and some small fraction of the four million filed every year will eventually be read by a public servant.
The bank pays the screening vendor which fires the alert, the bank pays the intelligence officer who reviews it, the bank pays the senior compliance analyst to spend a few hours collecting data from various employees and web applications into a single coherent narrative. And then the public pays the prosecutor to copy/paste the SAR into an indictment. (Accept this as a slight exaggeration, but if you can’t name a paragraph lifted from a SAR into a federal criminal indictment, you will be able to in about five minutes.)
FFIEC BSA/AML Examination Manual:
One purpose of filing SARs is to identify violations or potential violations of law to the appropriate law enforcement authorities for criminal investigation.
…
Examples of agencies to which a SAR or the information contained therein could be provided include:
A diligent public servant is welcome to use FinCEN’s database to get additional information on the subject of an existing investigation. But FinCEN will happily tell you the other sequencing works fine: trawl the database “proactively.” Most SARs are not evidence of crime! But if you have the choice between doomscrolling Twitter and doomscrolling the SAR database, one is much more efficient at converting into prosecutions. Their phrase for this is proactive SAR review and they have twenty volumes more if you are interested.
Very few Americans not professionally implicated in this surveillance regime understand it exists. FinCEN employees and bank compliance officers depend on it for their continued employment, and so it might be understandable why they are such effusive fans. But the regime does have informed critics, including occasionally this author.
One critique is that this regime is functionally an end-run around the Fourth Amendment. Civil libertarians have made this point for decades, but never with the economy of phrase as the U.S. Immigration and Customs Enforcement (ICE) internal magazine Cornerstone’s article The Currency Transaction Report: Controversial To Some—Essential To All.
Why is the CTR so useful to law enforcement, ICE?
ICE: ICE special agents utilize CTRs to establish links between individuals and businesses, and to identify co-conspirators and potential witnesses. This information is often utilized to meet the 'probable cause' requirement necessary to obtain search, arrest and seizure warrants.
Is this surveillance regime narrowly tailored?
ICE: ICE conducts approximately 1 million record checks of BSA data each year.
If a libertarian were scripting you right now they’d ask you to say that innocents have nothing to hide.
ICE: Individuals and businesses conducting legitimate transactions have no reason to avoid the filing of CTRs.
Yikes. Say, did you ever articulate the intentional double-bind twenty years before Bits about Money did?
ICE: However, criminals are forced to make a choice between appearing to be a legitimate customer, thereby exposing their assets and money movements through BSA reporting requirements, or engaging in risky, illegal actions to conceal the movement of their funds.
Wow, it seems like this field is filled with carefully laid traps that function exactly as designed. Did you by chance happen to publish the Hastert prosecutorial strategy ten years early?
ICE: Suspicious attempts to avoid the filing of a CTR by structuring cash deposits (making a series of deposits just under the $10,000 reporting threshold over a number of days) is a significant red-flag indicator of criminal activity and one of the most frequent triggers for the filing of a SAR.
Which brings us to the Southern Poverty Law Center (SPLC).
On April 21st, 2026, the Department of Justice unsealed an indictment of the SPLC for bank fraud.
The SPLC is a storied civil rights organization. Like many non-profits, it runs a portfolio of what are sometimes called “programs” under a single roof. One of those programs is producing a data product listing individuals and entities that it considers to be involved in hate and anti-government activities.
That data product is important financial infrastructure, and we will return to it in a moment.
The SPLC runs a private intelligence service to produce it. The SPLC has in the past paid informants, who it describes as “field sources.” Those informants are generally members of what it describes as domestic terror organizations. The existence of this program has been public knowledge for decades.
It is unlikely that any magistrate in the United States would approve a warrant to search the bluest-of-blue-chip civil rights organization's papers on the suspicion that they have created a fictitious CIA to launder money to the wife of an Exalted Cyclops of the Ku Klux Klan. Are you not aware, officer, that the reason this organization is in high school history texts is they developed a novel civil litigation strategy to bankrupt the Ku Klux Klan? You will not get your warrant. You would be lucky to escape court without a citation for contempt or an order for psychiatric commitment.
Well, good thing nobody ever had to ask for that warrant.
Banks don’t need warrants to become quite alarmed when they discover that they have created an account for the Center Investigative Agency and several other sole proprietorships for the same person… and those businesses don’t receive revenue, run payroll, buy office supplies on their debit card, or rent office space. No, the only thing they do is take large deposits then transfer out hundreds of thousands of dollars directly to, Great Scott, the worst people imaginable.
Substantially every employee of the financial industry, CEO or teller or product marketing manager that they may be, is obligated to attend a yearly training on their BSA compliance responsibilities. That training customarily requires you to pass a test. If that test stipulated this scenario and then asked what the financial institution must do next, there is only one correct answer: Conduct an investigation, close the accounts at issue with very high probability, and file a Suspicious Activity Report.
We return from this flight of fancy to the indictment. Excerpting verbatim:
Starting in the 1980s, the SPLC began operating a covert network of informants who were either associated with violent extremist groups, such as the Ku Klux Klan, or who had infiltrated violent extremist groups at the SPLC's direction.
If one does not closely follow this community of practice, one could be forgiven doubting whether prosecutors are being candid here. This claim does sound farfetched. The indictment, in this paragraph, is neutrally recounting the truth. The SPLC is proud of that program, which it ran for decades. NPR’s gloss:
The indictment came shortly after the SPLC revealed the existence of a criminal investigation into its disbanded informant program to gather intelligence on extremist group activities.
Well, OK, they ran an intelligence agency. One can construct a narrative by which that makes some tactical sense. Sure.
How did they get a bank to go along with making payments to people who the SPLC has spent decades attempting to make it impossible to pay. Did they perhaps… lie to a bank?
Indictment:
To secretly funnel donated money to the Fs, individuals at the SPLC, including a person who would become the Chief Financial Officer ("Employee-1") and a person who would become the Director of the Intelligence Project ("Employee-2"), among others, opened a series of bank accounts at Bank-1 and Bank-2 in the name of various fictitious entities, including, but not limited to, the following: Center Investigative Agency ("CIA"), Fox Photography, North West Technologies ("North West Tech"), Tech Writers Group ("Tech Writers"), and Rare Books Warehouse ("Rare Books").
Oh dear, SPLC! It would be extremely bad for you if you had in fact opened accounts for businesses which do not actually exist, then used them to move funds! Perhaps you can just pray that the feds never find out? … The bank is quite likely going to find out, though. Some bank accounts have red flags. These red flags have bank accounts.
Indictment:
In 2020, Bank-1 conducted an internal investigation into these accounts.
Oh that’s… unsurprising given the asserted facts. Well, your options are diminishing rapidly at this point.
Hey quick intermission: want a surprisingly reliable way to combat credit card fraudsters, drug dealers, and the like? First, you identify one of their accounts which is definitely committing crime. Usually they have lots of these and cycle through them quickly. They are often opened with synthetic or stolen identities. Burning the identity doesn’t get you all that much; they have thousands to cycle through. So just freeze the money in the account. Then, rely on human nature: nobody likes giving up “their” money. So compassionately offer to help them out, by offering to transfer the money from the frozen account to another account they control. We just need your quick written instruction to send your money to your other account, sir.
Indictment:
Thereafter, an SPLC employee requested that Bank-1 close the accounts associated with the CIA, Fox Photography, North West Tech, and Tech Writers and transfer the remaining balances in these accounts to a Bank-1 account ending in 6050 held in the name of the SPLC.
Industry practice varies on whether you give the user their money back before filing the SAR.
There are some grey areas in practice. You can’t return the money if you understand the user to be e.g. Hamas. You might be able to return the money if you understand the user to be e.g. engaged in unsupportable but debatably legal behavior.
“Unsupportable” here is a term of art: the institution, in its considered judgement, cannot allow it to happen on systems it controls. Many legal acts are unsupportable, and a determination of supportability is not and cannot be coextensive with a criminal conviction. Compliance officers are not federal judges and are happy to defer to them.
Please, we beg you, do not ask Compliance to run a parallel criminal justice system. We will do it if you force us to, but you will not like the outcome.
One of the functions of getting an explanation in writing from the SPLC (we will get to it; it is a doozy) is the financial institution seeks to absolve itself. Did we open accounts for cutouts to a domestic terrorism organization? If we did, *#%(, our regulators need to hear about that today. But this admission can be shared with a later regulator to say “We were unaware of the actual ownership of the accounts when opened and for ten years of use, which we agree is bad. We then executed our responsibilities with urgency. On the strength of this communication from the SPLC, which is not a terror organization, we decided to not immediately call you, and instead relied on the ordinary processes of our Compliance function. We will listen attentively if you feel we were ever derelict in our duties.”
One of those duties: a financial institution must, as a matter of black letter law (31 CFR § 1020.320), file a SAR if its investigation discovers a transaction designed to obscure the provenance of money. Transactions, by their nature, reference the account title (ownership, which could be by a e.g. company or trust) and beneficial ownership information (the ultimate people who have economic interest in the account). Any transaction conducted by an intentionally mistitled account is immediately and mandatorily reportable as soon as the financial institution has knowledge of this fact.
Alright, options for the SPLC are narrowing precipitously, but perhaps it can argue that those two employees, senior though they might be, were acting rogue? Or perhaps they could argue that the SPLC was institutionally unaware of the specific financial infrastructure its employees had created to support the SPLC’s intelligence program?
Indictment, quoting the President and Chief Executive officer of the SPLC, to the bank:
Pursuant to the discussion we had earlier this week, please let this correspondence serve as confirmation that the accounts listed below were opened for the benefit of Southern Poverty Law Center operations and operated under the Center's authority. The following accounts are listed below:
...6700 Center Investigative Agency — opened 1/31/2008, closed 8/5/2020
...9674 Fox Photography — opened 1/31/2008, closed 8/5/2020
...6743 North West Technologies — opened 1/31/2008, closed 8/5/2020
...6751 Tech Writers Group — opened 1/31/2008, closed 8/5/2020
...6719 Imagery Ink — opened 1/31/2008, closed 3/15/2013
...6727 J&J Electronics — opened 1/31/2008, closed 3/15/2013
...6735 Kelly's Marine — opened 1/31/2008, closed 3/15/2013
There are a variety of ways for the DOJ to get the CEO’s email. It may have been attached to a SAR, and therefore filed automatically with FinCEN. The other way, of course, is to pivot from a SAR (or any other reason to open an investigation) to a request that the bank produce records. Subpoenas are not strictly required; that document exists to exonerate the bank. A financial institution, concerned it is falling under negative government attention, might proactively offer to share what they know.
In any event, the feds got what they needed.
This written communication is a succinct confession to bank fraud.
There are multiple different ways to charge it, as we have seen. The indictment went with §1014. And if the SPLC admitted to bank fraud, then the transfers are wire fraud. And if the transfers were wire fraud, then the… you’ve seen this movie before and it ends predictably.
I do not expect this conclusion to be a happy one to all readers. I believe it to be correct.
There exist lawyers who say that the legal analysis in the indictment is sloppy. That statute is a weapon. Weapons wielded sloppily hit the target all the time. A weapon that only works when wielded perfectly is poorly designed.
Some commentators have implied theories that, for example, §1014 only applies to applications for loans. Excerpting the statute:
Whoever knowingly makes any false statement to… any [FDIC-insured institution]... upon any application… shall be fined not more than $1,000,000 or imprisoned not more than 30 years, or both.
This is extraordinarily broadly drafted, by design.The long list of alternatives to application includes loan, and as a basic principle of statutory construction, this means that Congress considered limiting the list to only loan applications and then intentionally did not do that.
In Wells, the defendant sold something of value to a bank, rather than borrowing money from them. (Turns out copiers print money, in a sense; you can sell the future revenue stream.) The lie was a relatively tiny detail relevant to the pricing discussion. Wells was prosecuted under §1014. The controversy was not “Does §1014 allow prosecution outside of loans?” Yes, read the plain text of the statute. But the holding is as interesting as the data point. Can you be convicted of fraud over a tiny lie? The Court held there is no materiality requirement under §1014. You can be convicted of fraud for a lie that doesn’t matter if you tried to influence any decision of a bank.
Some have advanced the notion that the account application is misleading but not false. This matters due to Thompson, decided last year by the Supreme Court, which holds that §1014 doesn’t cover misleading but true statements. Consider what happens when the prosecutor summons a senior SPLC executive to the stand and says: “So, Fox Photography, which you ran as a sole proprietorship. Did you buy a camera? Did you advertise? Did you file for a DBA? Did you make a website? Does Fox Photography have any activities other than this bank account application? You had three other businesses. Which of them did anything other than obtaining banking services?”
Some believe, plausibly, that the prosecution is politically motivated. Others might counter that the SPLC is the nation’s leading expert in lawfare and has just discovered sauce for the gander. Still others might believe both claims. Or they might believe “This looks like retaliation for the SPLC coordinating a coalition to interfere with Trump political fundraising,” which is not the way coalition participants say the SPLC gained his enmity [archive]. We will return, at length, to the activities of a coalition the SPLC co-founded.
Many commentators have argued that this program has been discontinued. Yes, bank fraud will frequently cease after its discovery. That is definitely a goal of this apparatus, and is almost definitionally true. Almost all white-collar prosecutions will happen after the conduct giving rise to them has ceased. The financial industry would certainly be chagrined to learn about a live fraud happening on its rails from the indictment. (That does happen; we have processes to detect it happening and then immediately investigate accounts associated with entities that were just indicted. We will discuss how data products and screening infrastructure function in substantial detail below.)
The industry as an institution expects its supervisors in government to bring these cases, all the time, against targets that have many friends, positions of authority, extremely competent defense lawyers, and sincere belief that they are innocent of any real crime. The government expects, as an institution, to be overwhelmingly advantaged in these cases.
Many commentators, including the government itself, have made this indictment mostly about the fraud against donors. Many believe that argument to be a stretch. I agree, unreservedly. As a connoisseur of this genre, I have read few documents which are simultaneously so far from the conventions while adding so little new to the canon.
It is a stretch that the government routinely makes and wins in other contexts. Matt Levine has collected several hundred examples of the genre, which he calls Everything Is Securities Fraud. That genre is, succinctly, “If you run a for-profit corporation, and have raised money from outside investors, and anything at all goes badly, and you did not describe exactly that thing to the investors as a risk, you have arguably defrauded your investors.” The government is comfortable making that argument and wins it routinely.
Perhaps Everything Is Donor Fraud. Perhaps not.
But, again, the design of this system is so you don’t have to prove the hard crime, the one where you’re being creative and taking some risks and pushing the envelope. You only have to prove the easy one, in exactly the same way hundreds of cases have won before. You will then use the spectre of conviction for (minimally) that as procedural leverage, and your target will likely settle.
Absolutely textbook.
A brief break from the SPLC’s situation. We’ll return in a moment. I had promised you a discussion about how the financial industry uses certain data products, including one published by the SPLC. We will begin with the canonical example of a data product.
As BAM has noted in discussing so-called debanking, the United States does not maintain a secret blacklist of people who can’t gain bank accounts. It maintains a public one.
Regulated financial institutions must deterministically reach the correct conclusion about accounts or transactions where they benefit certain people and organizations. That blacklist is called the Office of Foreign Asset Control (OFAC) list of Specially Designated Nationals (SDN). In broad strokes, this is a blacklist for foreign terrorists and narcotraffickers. (Banks aren’t the only people who can’t transact with the OFAC list. Reader, if you are an American, you can’t either, under penalty of law. But enforcement action is concentrated against banks et al because they are a, how might one phrase this, choke point for money movement.)
In theory, every time a bank opens a student checking account, it can have a bank employee mosey on over to the OFAC website, search the list in real time, and then determine that the prospective customer, yep, isn’t on the OFAC list. This is quite impractical and unlikely to be considered an acceptable set of controls by a regulator unless it is the smallest-of-small-town community banks.
You could write your own software to periodically download the list (yep, we just publish the files) from OFAC, and then compare new accounts and in-progress transactions against your recently-synced copy in your database. Most financial institutions do not choose to do this. It is fiddly, extremely high downside if you get wrong, and has zero financial upside if you do a better job than “minimally adequate.” Also, you have to do it many times redundantly across hundreds of functions of your financial institution. Checks, wire transfers, accounts payable, even your employee giving program! This set of considerations spells “outsource this function.”
The jargon for the function is “OFAC screening” and the company or companies which the financial institution engages to handle this are selling “data products.” You will work with your vendors and your internal IT teams to integrate those data products (which might be APIs, or platforms, or similar) with your other IT systems.
Then you turn everything on. Presto! You get alerts sent to Compliance if someone appears to be OFAC-listed. One of the large team of intelligence analysts you are forced to hire will be instructed to click through alerts as they stream by. The interface frequently resembles a Twitter feed from the most boring possible circle of hell.
Your analyst will tell the system to ignore the false positives (extremely common relative to true positives, but you basically have to look at every one) and action the true positives. “Action” here means close the account or block the transaction. A close synonym is “decision” the account.
If you’re technically sophisticated, you can probably configure your screening vendor to pass alerts off to some combination of heuristics, machine learning models, and other AI techniques before they are sent to a human. Alert fatigue is real and dangerous. You can decrease it by automatically decisioning low-risk accounts/transaction, based on criteria acceptable to your regulator, which you will write in your policies. Perhaps you have recorded that you have a U.S. passport or other evidence of citizenship on file for the account holder and therefore it is vanishingly unlikely they are the SDN whose citizenship is Farawayistan even if the names look similar. You might reasonably argue that, for retail accounts that are incapable of moving large amounts of money, that is good enough.
A bit of engineering and Compliance jargon: this architecture is a pipeline. An alert enters the pipeline from your screening vendor. It goes through some automated decisioning and routing to end up in a particular queue for a particular team of analysts. They decision the alerts which will, in some cases, be the end of it. In other cases, this will result in a new type of entry in a new pipeline, perhaps to effect the series of actions one must take to offboard an account. Pipelines are serviced by a mix of technical and human systems, and governed by both computer code and process documents written in English. Both the code and the documents are subject to review from your regulators. (They are far more likely to read the documents than the code, but they have essentially carte blanche to ask Compliance for anything they want that describes e.g. the OFAC pipeline, and Compliance will probably not push back very hard. Keeping a positive relationship with regulators is a very large portion of their job.)
The OFAC list is the canonical data product, but your screening vendor really wants to sell you several. Can you charge for a list the government makes freely available? Absolutely! Because the screening vendor isn’t simply charging for the list. They are charging for a complex technical and human system around the list.
One factor among many: you expect the list to change and you want them to be in charge of making sure you always have a very recent version. You also want them primarily in charge of understanding the e.g. regulatory environment around their data products. If one of the products goes from advisory to mandatory, you want to learn that from your vendor before you learn that from a pissed-off examiner wondering why you didn’t read the bulletin two years ago.
Some data products have very different characteristics than the OFAC list.
One example, alluded to above, is repackaging criminal indictments into a screening list. You might bank Bob’s Autos. If Beneficial Owner Bob is indicted as a money launderer for the mob, you want to know that very quickly so that no one e.g. drives off with the balances in Bob’s Autos’ accounts.
But you don’t have to close an account if someone is indicted, not like you have to close the account if they’re added to the OFAC list. It’s a judgement call, and you’ll have described your decisionmaking process for it in internal procedures documents, and your regulator will have blessed them. So one of your intelligence analysts gets the tweet-sized version of the indictment from the pipeline, reads “Misdemeanor assault”, and probably decides “Bob’s in trouble, certainly, but still supportable.” Or they read “Felony bank fraud” and that analyst very likely kicks off an internal investigation. Or, and again this is the dominant case, Close As False Positive. Turns out there are a lot of Bobs in the world who own car dealerships; that Bob was not our Bob.
Another data product is so-called “adverse news” screening. This one is not an extension of state power like the OFAC or prosecutorial lists, not directly. You have much more discretion on whether you buy it than you have on OFAC screening. But your screening provider might have gone to the trouble of licensing wire service articles or newspaper feeds or the Twitter firehose or similar. They repackage it and match e.g. mentions of colorful local businessmen (a classic newsroom euphemism for “mob, but we can’t prove it and he has lawyers ready to sue for defamation”) to your accountholders. If a colorful local businessman is reportedly on the lam and feared to have left the country, and then he asks for an international wire transfer, you probably don’t want to simply process it.
And now the data product you’ve been waiting for: the SPLC Extremist Files. Like the OFAC list, it’s available for free on their website, but there do exist screening providers which will happily charge you for it. Part of that work is for scraping, part of that work is for e.g. matching names to e.g. charity EIN numbers, etc. Your screening vendor will happily tell you, though, that the data product they’re selling you is really SPLC’s considered judgement, packaged in a way that makes it easy to include into your pipelines.
Why would you buy this data product? In part, it is because the financial industry broadly considers the SPLC an extraordinarily trustworthy non-profit. It is widely believed that if they say you’re a Nazi, you’re a Nazi, and we don’t want to do business with Nazis. Financial institutions, like other firms in capitalism, have broad discretion (with some specifically enumerated exceptions) in choosing who they do business with.
An aside to conservative and progressive critics of the SPLC: yes, I know, they are not as selective, restrained, and expert as their reputation suggests. But please accept for the moment that the financial industry understands this less well than you do.
One citation for the industry broadly considering the SPLC reliable and being aligned with their views on the good: JPMorgan Chase, the largest bank in the U.S., practically a metonym for conservative-as-a-banker, gave them $500,000 specifically to "work in tracking, exposing and fighting hate groups and other extremist organizations."
If you were to have a thousand conversations in the financial industry about non-criminal clients you don’t want to do business with, you would hear the SPLC cited more than any other group or data product.
Some of the most established screening providers do not carry the SPLC data product, though they have data products which compete with it. The SPLC has in the past criticized those providers by name:
World-Check is often criticized by civil rights organizations, advocates, and experts on international terrorism for bias and misinformation that can result in the blacklisting and de-platforming of legitimate charitable groups. The commercial nature of World-Check, its lack of coordination with civil society organizations, its use of unsubstantiated data, and its lack of transparency make it a highly problematic tool to screen out hate.
In substance, the SPLC’s complaint is that our competitors list people we wouldn’t, don’t list people we would, and we’re just better at this. Which, fair enough, everyone is allowed to have an opinion.
How did we arrive at the position where financial institutions clamored for their data providers to offer SPLC screening? Marketing and sales are skills and the SPLC is very, very good at them. Also, again, read a history book of your choice; they picked a fight with the KKK and won. If you get a reputation for doing that for decades and also have an aligned product many customers feel the need for, sure, they will want to get it from you specifically.
That is not the only reason why many people in tech companies, financial infrastructure companies, and banks are intimately acquainted with the work of the SPLC. We will return to the other reason in a moment.
But, what does your SPLC pipeline do? Depends! Perhaps alerts go to an analyst, who checks it for false positives (yep, hits will frequently be false positives), and in the case of true inclusion you have a spirited debate within your firm. Perhaps some people argue that even Nazis need to eat, and to eat you need money, and that on balance the marginal harm of giving this particular Nazi a checking account is outweighed by the social utility of their children not starving to death. You are consuming the SPLC’s data product on an advisory basis; your firm retains full control of decisioning.
Or you could configure your pipeline to automatically deny services to anyone the SPLC lists, either by operation of computer code or by the programmatic-but-in-the-sense-of-directing-humans way that many processes still work in the financial services industry.
Jeff Bezos, in Congressional testimony, describing Amazon's reliance on the SPLC data product for AmazonSmiles, a now-discontinued charitable product they offered:
"We use the Southern Poverty Law Center data to say which charities are extremist organizations. We also use the U.S. Foreign Asset Office [sic] to do the same thing.”
Bezos was interrupted before he could finish his next thought; you're welcome to read the testimony for full context. He is clearly referring to the OFAC SDN list.
Bezos went on to elaborate that the Fortune 2 company could not operate AmazonSmile without some way to kick out the extremist organizations and that SPLC was, effectively, the only reasonable option. He asked Congress for other suggested data providers. None were offered. (No, really, he did that.)
Let us pause to acknowledge that Bezos, one of the richest men in the world, considers these two four-letter organizations as peers. One of them is created by statute, operates within constitutional and administrative-law constraints, and answers to Congress, the courts, and ultimately the people of the United States of America. It could jail Bezos, personally, for willful non-compliance. And the other is …some people in Montgomery with a very specific interest, whose decisions are subject to review by no court, and whose only power appears to be moral suasion.
Bezos was equally and entirely committed to satisfying both.
Why? We’ll return to it in a minute.
As a longstanding financial infrastructure enthusiast and practitioner, I am confident that SPLC screening is used on an advisory basis in very many sectors of the financial industry. It is also used in a delegated authority fashion for some products at some firms, in the fashion that Amazon used to. In the delegated-authority cases, an SPLC hit kills an account application or transaction as cleanly and automatically as an OFAC hit does.
Perhaps that strikes readers as implausible, even after you just heard it in sworn testimony to Congress. I offer to you publicly documented examples, frustrated that they all cluster in a small set of the vast panoply of financial products. There is a reason for that clustering, related to the SPLC’s marketing and sales motion, and we will discuss it in a moment. A warning: if you assume the public examples are fully representative of the SPLC’s delegated authority you will materially underestimate how much actual power the SPLC has over financial infrastructure.
Many employers in the United States offer a perk: if you donate to charity, we’ll match what you donate, up to some dollar amount and subject to some restriction. This is, morally, compensation, just like the salary is compensation, just like the 401-k match is compensation, just like the healthcare benefits are compensation. Firms use specialist providers of financial services to run payroll, administer 401-k plans, and deliver health insurance.
Deed offers a workplace giving program as a service (WGPaaS? We’ll workshop it.) Some Deed customers are banks, and so they have a ready answer [archive] for your Compliance people on the work Deed already does on your behalf: Continuous Monitoring: Stay protected with up-to-date screening against sanctions and regulatory watchlists, including IRS, OFAC, SPLC, PEP, and adverse media.
One of these acronyms is not like the others.
This perk is quite popular in banks, who have been trying to shake the heartless image since the Medicis, and who want people to feel good that they teleport value through time and space but also really and truly care. So some financial institutions in the United States, possibly without knowing it, may have, in delegating authority to Deed to decision requests for compensation, indirectly delegated it to the SPLC.
I assume, as enterprise-grade software, that many workplace giving programs have many levers available to customers if they want HR to review every match of a $20 donation to someone’s parish. As a self-evident statement of prioritization: no, HR does not want to do this, at all, ever, please stop wasting my time, configure it the way you do for every other bank. Do you expect Customer Success to press on and say “Nope, sorry, not enough to proceed. Is being able to donate to Nazis important to your employees?”
An observation from someone who worked in the marketing department of a financial services company: features on the industry-specific solutions page are there because customers care about them and not having them is a dealbreaker. So you must offer the SPLC screening to customers. But it is socially impossible to ask whether they want it. Product decision time: what is the default value of the Allow Gifts to Nazis checkbox.
Now, a quiz: do you think Compliance at a bank is neutral on “Can the bank delegate transaction-level decisioning authority, in any part of the business, however small, to an entity under federal indictment for bank fraud? Does the answer change if they are convicted of bank fraud?”
No! Compliance will not let you do that! Not because they are worried about the integrity of the blacklist. An accused bank fraudster has the final say to approve money movement out of a regulated financial institution. That is very likely intolerable to Compliance.
What happens next? Well, remember, when you bought the data product, you were also buying someone anticipating your concerns before you even voice them and preparing options before you ask. Jeff Bezos’ words echo in San Francisco today: Does anyone know another option?
Deed is not an outlier in workplace giving programs.
Groundswell? The FAQ recently read “Groundswell does not process donations to organizations denoted as hate groups by the Southern Poverty Law Center.” but changed to “Groundswell conducts due diligence to confirm they meet applicable IRS standards. Clients can also configure their own charitable restrictions within Groundswell, including allowing or blocking specific organizations or categories of organizations, in accordance with their internal policies.”
No prizes for guessing the default.
Millie? Blog: "Vetting nonprofits can be a time and labor sensitive task… That is why vetting is typically left up to the experts at SPLC. All vetting for the Millie database is even through the SPLC!” [sic throughout] [archive]
And, again, you are reading the tip of the iceberg. There is much more use of the SPLC list in the financial industry, in much more important products than workplace giving.
Why is it so easy to find public evidence in giving programs but not of SPLC blacklisting in e.g. life insurance or wire transfers or options trading?
The SPLC and its allies bootstrapped a consensus in their core community of practice, non-profits and the supply chain that funds them. I will describe the shape of that consensus without making specific claims about truths. It is: either you’re screening charitable donations for hate funding, or you are a monster. You will not attend our parties. You will not get our retweets. You will be iced out of the flow of money, because we have friends at Ford. One phone call and Open Society is closed to you. And then good luck paying your staff. We have spent our professional careers getting very good at delivering social consequences through tightly coordinated coalitions. Get with the program, or get consequenced.
If you want to understand why the charitable giving world moves in lockstep here, start with the Amalgamated Foundation's "Hate Is Not Charitable." You will find it a project to reconstruct what that did, but the SPLC has a whitepaper with most of the important story beats.
It's a long story, and I would rather tell you a different story, about how the SPLC formed a coalition to gain account- and transaction-level decisionmaking capability at tech companies, financial infrastructure firms, and banks through a coordinated pressure campaign.
Parts of this story are abundantly reported in public. Parts are extremely well understood in the organizations that the SPLC’s coalition repeatedly persuaded, cajoled, or threatened (pick your favorite verb for the moment).
Some parts of the story are original public interest reporting. What is the public interest in candidly recounting the exercise of power over Nazis? Because they did not stop once they achieved power over the Nazis.
One coalition of non-profit organizations ran an organized pressure campaign against industry, for years. It started in 2017, with the SPLC and another non-profit informally coordinating. It intensified and formalized in 2018, under SPLC co-leadership. It escalated sharply in 2020 and 2021.
The campaign had two main components. The first was public advocacy and communications work. The second, less visible but more consequential, was a series of meetings with industry. Hundreds of meetings. With a specific target set of companies.
The campaign's declared aims were three. To convince those companies to censor more communications the coalition characterized as hate. To blacklist organizations and individuals the coalition characterized as promulgators of hate or violence. And to interdict the flow of funds to those blacklisted parties.
The coalition claimed to be non-partisan. Be on the lookout for mentions of “non-partisan,” because it is a word the coalition understands differently than I do.
The coalition calls its targets “Internet companies” and relies on government, media, and the public to not read the fine print. In it, they define Internet company mendaciously to include banks, credit card processors, and any other financial infrastructure their enemies could touch. The coalition was going after posts, but it was also and primarily going after money. I will use the language “industry participants” going forward to identify who they met with.
Industry participants included Facebook, Twitter, JPMorgan Chase, Visa, Mastercard, and many other firms. Some were among the largest companies in the world. Others had fewer than 10 employees. (I estimate headcount based on published reporting and industry experience.)
Stripe was an industry participant. I was employed at Stripe continuously from late 2016 through early 2023, covering the entire period under discussion. I remain an active advisor to Stripe. Stripe does not necessarily endorse what I write in my personal spaces.
This series of hundreds of meetings involved hundreds of employees from industry participants. Those employees included C-suite executives and managers and individual contributors across a host of functions. Those functions included communications, legal, government affairs, Trust and Safety, and compliance professionals.
Meeting notes were frequently kept, and sometimes widely circulated, as is the routine practice in industry. The meetings were documented on calendar invites (often with full participant lists), shared docs, attachments, emails, and other contemporaneous records. In the ordinary practice of industry these primary documents distribute themselves promiscuously into secondary documents; think of an email being screenshot to paste into a PowerPoint to discuss the response in a meeting. Records exist on conservatively hundreds of systems and can be accessed by many more than 10,000 people.
No employee of an industry participant I have spoken to, familiar with the contents of the meetings, was willing to provide quotes for publication with their name and corporate affiliation attached.
Their reasoning included not being authorized to disclose private information, fear for their personal and corporate reputation, future career consequences for leaking, personal consequences for being identified adjacent to national political controversies, in some cases fear for their physical safety, and in some cases unwillingness to betray a cause they personally support.
Industry participants recount the tone of the meetings differently, and as varying over the meetings. Some meetings were strained-but-professional. Sometimes the coalition participants were described as demanding and “hectoring.” Industry participants report abusive remarks towards their companies and to the people in the meeting.
Industry participants were repeatedly told that if they did not accede to demands they would be profiting from evil, complicit in the death of innocents, or benefitting from white supremacy. The innocents claimed to be at risk were often specifically identified as black, including during a period of intense societal concern for the lives of black Americans specifically. Industry participants were told that they wanted this. That they were taking “blood money”. Industry participants repeatedly felt personally attacked, in ways and using language not normative in their professional experience.
On the account of multiple industry participants, coalition participants explicitly held individuals in the meeting personally responsible for the actions of their employers. This was aimed at individuals with substantial influence and authority in companies, and also at junior employees.
Industry participants describe the coalition participants as threatening their employers, openly and by implication.
The most commonly described threat was coordinated negative public messaging with the goal of causing reputational harm to the industry participants. Feared comms outcomes ran the gamut from heavy mainstream media coverage to a Twitter pile on. Twitter is real life, particularly when a large and vocal contingent of your employees use it and Slack simultaneously. Ever been pulled into a meeting over a single customer tweet then burn weeks on managing the fallout? Count yourself lucky.
Less commonly, the industry participants perceived they were being threatened with adverse legislative, executive, or regulatory action indirectly by coalition participants who are reasonably read as exercising substantial political influence. Industry participants sometimes report that coalition participants flaunted their political influence.
Industry participants were repeatedly told that if they did not accede to specific demands, they would share the blame for future deaths. Bits about Money has reviewed contemporaneous records which unequivocally make this claim, authored by coalition participants. We note that this echoes language the coalition routinely puts in press releases, Medium posts, and similar artifacts after presumptively careful review of the phrasing. The coalition was inconsistently disciplined in phrasing in documents we have reviewed, and we decline to quote their phrasing, in part, out of charity.
You will share the blame. We will hold you responsible.
The coalition has publicly and voluminously described their own understanding of what was said in those meetings.
Where employees of industry participants dispute their characterizations, I will characterize broadly what some employees of industry participants have said, to preserve their anonymity. You should not view this as a claim on behalf of all industry participants. Patterns emerge frequently, but I am making no claims about unanimity.
Many left-of-center voices felt that white supremacists had been emboldened by the 2016 election of Donald Trump. Beginning in mid-2017, Color of Change communicates with and meets with PayPal, with the objective of cutting off financial services to hate groups. Color of Change is a civil rights organization which specializes in online organizing.
The Center for Media and Democracy, an aligned non-profit, quotes a senior executive as saying “Let’s be clear: public speech promoting ideologies of hate always complements and correlates with violent actions.”
Industry participants characterize the coalition participants as asserting that speech was inseparable from conduct. Free speech concerns were dismissed and, industry participants report, mocked, including with the dismissive rendering “freeze peach.”
As has been abundantly reported elsewhere, a coalition of white nationalist, neo-Nazi, and alt-right organizations (per voluminous public reporting tracking self-identification) organized a rally in Charlottesville, Virginia. This sparked counter-demonstrations. A rally attendee struck and killed a counter-demonstrator with his car.
Color of Change intensified its existing engagement with PayPal and other industry participants. Rashad Robinson, then executive director, would describe them in detail later, to a podcast on iHeartRadio. Fast Company [archive] approvingly cites that this came after “Robinson used similar tactics to move companies to withdraw sponsorship from the 2016 Republican National Convention.” The Republican National Convention is a get-together sometimes described as a grand old party.
Robinson articulated the coalition’s theory of change: “Power is the ability to change the rules.” The coalition perceived the industry participants as having power, desired power for itself, and took steps to achieve it.
Color of Change swiftly organized what it describes as a social media campaign using the hashtag #NoBloodMoney.
In the wake of Charlottesville, which was shocking in the broader U.S. political environment and perceived as a watershed moment within tech companies, many industry participants made decisions to end services to a variety of groups they felt had violated their policies against promoting violence or extremism. This was sometimes proactively. It was sometimes after receiving communication from activists, either in their personal capacity or identified as coalition participants.
Meetings were, prior to this point, relatively ad hoc. This would soon change.
As mentioned above, the SPLC enjoyed broad trust within the financial industry dating to long before these events. Chase’s donation to SPLC immediately after a galvanizing tragedy could, if one were immensely cynical, be read as a tiny communications expenditure.
Industry participants routinely claimed shock and a sense of urgency after Charlottesville. A grown man once wept in my presence recounting that event. While there is substantial diversity of views among industry participants, many have, in their private spaces, when the cameras are not rolling, when there is nothing to gain, repeatedly described the SPLC to me as being on the side of the angels.
Keep this in mind as the coalition describes industry as being standoffish and foot-dragging.
The SPLC co-led an effort to unify, coordinate, and intensify previously ad hoc organizing actions. Change the Terms (CTT) was a coalition, to its friends, a conspiracy, to its enemies, and an unincorporated association, to a geek with an unhealthy interest in LLC formation. (The only fact I’ve ever retained about unincorporated associations is that they are jointly and severally liable for acts of the members.)
The individuals identified contemporaneously as co-chairing CTT were Heidi Beirich (then-head of the SPLC Intelligence Project) and Henry Fernandez, of the Center for American Progress (CAP).
SPLC’s Intelligence Project ran the private intelligence service and produced its data products. It also produces an annual intelligence estimate, such as the (2024) Year in Hate and Extremism.
(Beirich left SPLC in 2019 to co-found Global Project Against Hate and Extremism (GPAHE) with a fellow SPLC alumna.)
The SPLC characterized the CTT coalition as its own initiative under the Intelligence Project, and not simply Beirich’s initiative, in charitable governance and fundraising documents in the possession of Bits about Money. We cite one such document below, contrasted against later Congressional testimony.
According to documents reviewed by Bits about Money produced by coalition participants, the SPLC participated in cost-sharing arrangements to fund expenses of other coalition participants incurred in carrying out the joint purpose of the coalition. We are unaware of the extent of this practice.
CTT presently describes its most senior members as CAP, Color of Change, Common Cause, Free Press, GPAHE, Muslim Advocates, the National Hispanic Media Center, and the SPLC. There is some ambiguity around who claims founding member status and whether that list has evolved over time. Startup life, I get it.
I will refer to CTT’s primary artifact as the Terms. This document, announced at the coalition’s debut, was foundational to CTT’s positioning (they are Change the Terms). The Terms were sometimes described as recommendations, sometimes as a model Terms of Service (ToS). They were consistently positioned as being for Internet companies.
This is sleight-of-hand. A primary purpose, perhaps the primary purpose, of the Terms is to interdict money movement.
The Terms define “Internet Companies” in a non-standard fashion to include banks, credit card brands, any business of any character which facilitates a transfer of money with a web or mobile interface, and also more central examples of Internet companies. This is in keeping with the coalition’s by-now demonstrated target selection of PayPal (an Internet company) and Mastercard (which predates the commercial Internet by decades).
The SPLC co-drafted the Terms.
The SPLC referenced the Terms in Congressional testimony as being an extension of the SPLC’s long-running campaign to interdict money movement to targeted organizations.
For decades, the SPLC has been fighting hate and exposing how hate groups use the internet. We have lobbied internet companies, one by one, to comply with their own rules to prohibit their services from being used to foster hate or discrimination. A key part of this strategy has been to target these organizations’ funding.
The Change the Terms coalition existed to coordinate and parallelize execution on this tactic. In addition to nominating targets for existing policies, it extracted concessions from industry in the form of policy changes. The coalition, when minimizing its own power served its purposes, sometimes described all actual decisions as made by industry. The coalition was very candid when speaking with itself, with allies, and with industry participants. The coalition understood itself to have some degree of coercive power, and factually had some degree of coercive power, as we will discuss. It also secured delegated authority, routinely but not universally, as we have discussed.
Industry participants do not consider the Terms to be reasonably characterized as a ToS.
I would say the Terms are an advocacy artifact which adopts the stylization of a ToS without making any effort to be one. A ToS is a binding contract that industry customarily pays professionals to produce or adapt from firm-maintained templates appropriate to young startups. The English-language U.S. ToS of a major tech company has consumed more than 7 figures in bespoke services work, as a rule. The idea that a filesharing service and regulated U.S. depository institution could adopt the same ToS is fatuous on its face.
The purpose of the Terms was to get the meeting and, oh boy, did the coalition get them. I estimate they successfully achieved hundreds of meetings.
Color of Change’s Robinson was interviewed by Hillary Clinton on her podcast You and Me Both in March 2021. You and Me Both is available on major podcast platforms through iHeartRadio. Readers may recognize Clinton from other work.
Bits about Money has archived the podcast MP3 file, to make specified quotations findable via timestamps. Many professional podcasts use dynamic insertion of ads, which is good for advertising revenue but bad for reproducibility of timestamps across listeners. Please do not use the archive unless you need these specific timestamps.
Robinson confirms that CoC works with SPLC and that its relevant work began after the 2016 election (29:15).
Episode at 29:30:
We started calling the credit card companies. We started calling these payment processing companies. And you know what they told us? They said, oh, we're with you, but, you know, you have to talk to the banks. And then the bank said, you know, you have to talk to the credit card companies. So we start building the #NoBloodMoney campaign and we start building this platform. And, you know, we're not quite done with it all when Charlottesville happens.
Robinson describes a central tactic of the coalition: identifying particular accounts it wants deactivated, with a consequence if demands are not met. He claims this to have been demonstrably effective.
Multiple industry participants describe the same sequence of events across several invocations of the tactic. I feel it necessary to caveat causality, as described below.
Episode at 30:00:
We have been talking with you [companies] for months. We’ve given you these lists of white nationalist groups. And then within about twenty four hours [of launching the #NoBloodMoney campaign], they start sending us a list of white nationalist organizations that they are cutting off from processing. No law had changed.
Clinton interjects: Exactly.
Robinson locates this within his non-partisan broader political project.
Episode at 28:00:
We really built what I feel is a new strategy. It was focused not simply on resistance, but on opposition. What would it mean to not just resist but to build power, to oppose, so that we could get back to governing, focusing on winning real victories at the local level, while also recognizing that the game was not fair, that the rules were rigged, and that we couldn't simply say that what happened in 2016 was democracy. It was what happened.
Clinton later comments, at 31:20 :
Moving [your advocacy] to the private sector, and corporate power, was an incredibly smart approach.
Industry participants have, compared to anyone else in the world, broadly better information about account status, account history, position in pipelines, and similar. (This is not to say they have total awareness of all information in their possession, or that all employees of an industry participant have equivalent access to information and capacity to understand it. Some organizations tightly silo information internally by role.)
It is easy to infer causality from timelines without that being warranted. One mechanism for this: accounts may be in pipeline at the time of target nomination. An external observer will perceive “account active, nomination communicated, account closed shortly thereafter” and make the obvious inference.
If one understands one’s counterparty to have misunderstood something, one can correct them. Or not.
Industry participants describe a variety of tactics for extending olive branches to the coalition participants, including but not limited to acceding to demands. One such tactic was giving more visibility into pipelines than the broader public had, with or without influence on operation of those pipelines. “Thanks so much for bringing that to our attention. They are absolutely on our radar now.” can mean many things, including “Message received.”, “I confirm they are in pipeline.”, “I confirm they are in pipeline thanks to you.”
The CTT Terms include the following recommendation.
Many Internet Companies have granted special exemptions to official accounts, government actors and powerful people, allowing them to promote hateful activities, disinformation and other divisive behavior. Instead, these actors should be held to the same standards (if not higher standards) as regular users. There should be no special exemptions that allow the powerful to spread hate with impunity. Many official accounts at various social-media companies have circumvented platform policies despite promoting hateful activities, disinformation and other divisive behavior. Policies should apply equally to all users and must be enforced.
Industry participants perceived themselves as being in an impossible situation with regards to a handful of accounts which were both extremely vexatious to coalition members and obviously newsworthy. Consider how manifestly unwise it would be to intentionally deplatform the sitting, duly elected President of the United States. While nominally about a large class of users, industry participants describe the motivating examples brought up in meetings as consistently circling back to Trump, Tucker Carlson, and a very short list of other names.
The ADL, a coalition-aligned non-profit, co-authored a press release with some coalition members titled Deplatform Tucker Carlson.
The coalition benefits from the mistaken impression that it only asks platforms to remove accounts controlled by terrorist organizations. No. The first, unobjectionable list is the ante. After you’re in the hand, they raise you Tucker.
Once the coalition has achieved agreement in principle it defines the bounds of polite society, it soon broadens the ask, framing the new concession as something you have already committed to publicly.
The coalition often communicates the ask privately but the retaliation for non-compliance publicly. The public, mainstream media sources, and similar interpret the sudden coordinated pressure intensification as evidence that the targeted company has failed at the original commitment, the one about terrorist organizations.
In public communications, some coalition participants exhibit message discipline in locating the agency within the industry participants: the coalition “recommends” policies, the industry participant agrees to a policy, then the industry participant is responsible for enforcing what is now their own policy.
Coalition participants were, in the recollection of many industry participants, frequently undisciplined in meetings. They specifically nominated accounts for adverse actions, up to account closure, in no uncertain terms, and it was not a request.
Color of Change, at a minimum, was quite disciplined: they consistently adopted coercive conditional escalation as their default engagement model. Get the meeting, communicate demand, show a marketing brief of words and images that would be activated if you did not swiftly accede to the demand. This account is described by industry participants and by executive director Robinson to Fast Company, where he describes employing it “95% of the time.”
Coalition participants were inconsistently disciplined in their contemporaneous written records, some of which Bits about Money has reviewed. Authenticating these as true copies is tricky; authenticating public statements is not.
The Leadership Conference on Civil and Human Rights in October 2019 wrote Facebook a public letter, which the SPLC and many coalition members co-signed.
And yet, sabotaging your own efforts, Facebook recently announced that it would automatically deem speech from politicians to be newsworthy, even when it violated the company’s Community Standards; exempt politician-created content from its fact-checking program – permitting anyone running for office to post or purchase ads with falsehoods; and exempt content deemed to be “opinion” from its misinformation rules. Politicians should not get a blank check to lie, incite, spread hate, or oppress groups of people. Politicians are historically responsible for perpetuating discrimination and erecting barriers to voter participation, while autocrats throughout history have relied on mass media to rise to power and subjugate minority communities.
Note the conflation here of committing incitement (illegal), spreading hate/oppression (probably bad), and lying while being a politician (Tuesday). This sort of conflation, of attempting to box someone into a proposition they had never actually agreed to, was routine, in the view of some industry participants.
I contemporaneously viewed the brouhaha about politicians lying as being battlespace preparation for the 2020 election. First, establish the general principle that social media platforms had a duty to censor lies told in campaigning. (This was sometimes described as “misinformation,” to imply that an American politician lying was doing so in a Russian accent.) Then, seize on every lie in one very specific political campaign, and use the platforms to interdict that political campaign’s storytelling. I didn’t expect campaign financing shenanigans, because I have a strong prior that responsible professionals might fly close to the sun but do not attempt to fly through it. More on that later.
Industry participants have their own compliance issues to worry about and frequently perceived this two-step as being too cute by half. The aim was obvious to them. Industry participants describe coalition participants as stating directly that Trump lies frequently, and helpfully telling people with degrees in logic that it therefore follows that if lies cause decisioning, and Trump lies, Trump should be decisioned.
The SPLC has described the coalition's strategy in its own voice, in the most formal venue available to it: sworn testimony before Congress. Lecia Brooks, who self-identifies as senior SPLC leadership, appeared before the House Financial Services, Subcommittee on National Security, International Development and Monetary Policy on January 15th, 2020.
Verbatim quotes from prepared testimony:
For decades, the SPLC has been fighting hate and exposing how hate groups use the internet. We have lobbied internet companies, one by one, to comply with their own rules to prohibit their services from being used to foster hate or discrimination. A key part of this strategy has been to target these organizations’ funding.
The coalition was an extension of the SPLC Intelligence Project, identified as such in their 2018 Annual Report, pg 9 [archive]. A charity annual report is a governance and fundraising document exhaustively reviewed by professionals and customarily approved by the board. It would be uncharitable to argue the SPLC misunderstands or is dissimulating about its role in the coalition in that document.
Brooks, to Congress, chooses to describe the SPLC as a member of the coalition and not the animating force of it:
On Oct. 25, 2018, the Change the Terms coalition – including the SPLC and other civil rights groups – released a suite of recommended policies for technology companies that would take away the online microphone that hate groups use to recruit members, raise funds and organize violence. In response to Change the Terms’ advocacy, several Silicon Valley leaders have made promising changes that align with the coalition’s vision for a safer online world.
Brooks then lists several examples of specific wins the coalition achieved.
Brooks then claims these accomplishments advanced the SPLC’s mission. She implies that the coalition’s important work will continue.
Hate groups have clearly been damaged by the efforts of the SPLC and its allied organizations, including the Change the Terms coalition, to fight them and their funding sources online. But the fight is far from over.
Brooks had an opportunity to describe industry participants as valued partners. Brooks describes the SPLC’s relationship with industry participants in part as follows:
The public exposure was half the battle. We conducted the other part of the campaign privately. SPLC officials held dozens of meetings with top Silicon Valley executives. Some companies acted. Some took half steps. Others did little or nothing. But eventually, the far-right extremists who depended on Silicon Valley were beginning to feel the pain.
Brooks characterizes the SPLC’s tone in a similar fashion to industry participants quoted above.
She indirectly confirms one of the campaign’s core tactics: get the meeting, get a commitment under threat of coordinated public pressure, then judge progress against the commitment to be inadequate. In the next meeting, offer absolution and de-escalation, contingent on policy concessions. Repeat as desired.
The SPLC kept up the pressure, cajoling companies and exposing those that dragged their feet.
The coalition, across a wide variety of documents, more consistently describes itself as having only influence when having power would require accountability, and more consistently describes itself as having power when addressing audiences presumptively sympathetic to the aims towards which that power was deployed.
As a reminder, in late May 2020, the death of George Floyd triggered a wave of nationwide protests.
Several of those protests devolved into riots and looting. This continued for months. The usual reckoning of the death toll, based on contemporaneous reporting, is two dozen. Property damage is generally estimated at between $1 and $2 billion based on insurance industry claims data.
Trump posted “Any difficulty and we will assume control but, when the looting starts, the shooting starts.”
The U.S., unfortunately, has long historical experience with race riots, and the civil rights movement has strong institutional memory of that phrase being invoked to justify murder as a riot control tactic.
One can believe people steeped in this tradition, inclusive of many coalition members, sincerely understood the post to be a true threat. One can also believe they understood the situation to be an opportunity.
The coalition’s operating logic has been to use each expansion to prepare for the next. A win here would establish that no one is beyond its reach. It would also establish that industry just isn’t qualified to understand what their policies mean, and should defer to the subject matter experts who wrote them.
Facebook declined to remove the post.
Some employees at Facebook organized a walkout in protest.
In an attempt to quell the discontent within the ranks, senior Facebook leadership (Zuckerberg and two lieutenants) had an unusually publicized meeting with coalition members (the heads of Color of Change, the NAACP, and the Leadership Conference on Civil and Human Rights).
Coalition participants did not achieve what they professed to want in that meeting and, in a tick-tock motion industry participants were very familiar with by this time, released a statement to media then coordinated coverage around it.
Widely quoted language from the statement included “Mark is setting a very dangerous precedent for other voices who would say similar harmful things on Facebook.” The specificity and analytical rigor of this sentence is not dissimilar to that recounted by industry participants of statements made in many meetings.
The statement explained its concern was that failing to censor Trump, in a non-partisan manner of course, would result in voter suppression, via a causational pathway that the margin of the statement may have been too small to contain.
This was transparently designed to activate commitments Facebook had made in the wake of the 2016 election.
Believing the 2016 election had been tainted due to Russian interference was a left-coalition signifier—much as believing Trump actually won 2020 became a right-coalition signifier later. Neither of these views has the evidentiary strength the coalitions claim for them. But they aren’t claims advanced to achieve understanding; they are advanced to achieve alignment and, through it, power.
If one was concerned about the substantive merits of the claim on election interference, and not willing to simply accede to it on the strength of the speaker’s social position, one might wonder whether widespread actual violence might not suppress voting more than words describing hypothetical government violence.
Industry participants who asked coalition participants (in other circumstances) to explain their reasoning were told that it was not their job to educate them, that there exists literature, and that civil rights organizations had unmatchable expertise. Stick to coding, geeks. This did not always mollify industry participants, who in 2020 and 2021 were becoming deeply skeptical of expertise wielded as a shield for disastrous policy recommendations. For reference, see any history of the early days of the covid pandemic.
When they knew the cameras were rolling, participants were fractionally more disciplined. Color of Change's Robinson delivered a 2019 speech to Facebook leadership [archive], telling executives directly that they had 'profound gaps in their expertise' and that implementing CTT would be 'a step toward seriousness.' We believe we fairly characterize other documents we have seen as extending the logic from a claim about incapacity to understand racism as a societal problem to incapacity to understand the words written on industry’s internal policy documents.
The term of art in industry for the person responsible for the interpretation of a document is the “owner” of that document. Accepting this term of art, many professionals in the industry would agree that if the coalition doesn’t understand themselves to own the policies, it’s tough to guess where they think they should be on the stakeholder-analysis form. “Consulted” doesn’t get to say the owner has blood on their hands after a decision.
The House Judiciary Subcommittee on Antitrust, Commercial and Administrative Law conducted a hearing on Online Platforms and Market Power, Part 6: Examining the Dominance of Amazon, Apple, Facebook, and Google. The CEOs of the four companies attended as witnesses.
This is the hearing at which Jeff Bezos invited Congress to recommend a substitute data product for the SPLC blacklist.
About a month later 15 Republican lawmakers wrote Bezos a letter, saying:
Amazon’s ongoing reliance on the SPLC, with its documented anti-conservative track record, reinforces allegations that Big Tech is biased against conservatives and censors conservative views.
The letter did not contain a recommendation for an alternative data product.
Industry participants were extremely aware of the climate regarding potential anti-trust actions against their firms at many times during these years. Avoiding that was a central goal of policy teams and company leadership at all levels. Industry participants perceived the coalition members as possessing substantial influence over outcomes for anti-trust policy.
You don’t get interviewed by Hillary Clinton for being a nobody.
Joe Biden won the 2020 election. Trump disputes this.
A planned demonstration in Washington D.C. for protesters sympathetic to him, timed to coincide with the counting of electoral votes in the Capitol Building, devolved into a riot. Demonstrators gained physical access to the Capitol Building, sometimes by force and sometimes being let in by overwhelmed police. Capitol Police shot and killed one demonstrator while she attempted to enter a window. A Capitol Police officer who had responded to the riot died the following day; the medical examiner ruled the cause natural (strokes) but noted the events of the day played a role in his condition.
Industry participants and coalition participants treated the events of January 6th as a multi-faceted emergency and responded within days.
Industry participants converged on nearly unanimously terminating or severely restricting services to Trump and affiliated entities. Coalition participants pressed publicly and privately for this outcome.
Some commentators view these events as over a dozen firms watching the same news and making substantially the same decisions independently of each other. Some commentators, focusing on the near unanimity, believe these decisions to have been strictly coordinated. This commentator believes neither.
There was a widespread effort to blame the tech industry specifically for the events of January 6th, contemporaneously reported in many places. The WSJ synthesizes, in a straight news story, the view “The Capitol incursion, some of which was planned and discussed in advance on social media, has hardened many Democrats’ view that a lack of tech-platform regulation is undermining democracy.” The climate in industry contemporaneously was acutely aware of being perceived as a threat to national security.
Industry participants perceived they were making decisions under conditions of profound risk to their businesses. This perception was contemporaneously noted by many external observers, including then-Senator Rubio, quoted by the WSJ as saying:
The reason why these guys are doing it is that the Democrats are about to take power, and they view this as a way to get on their good side.
If “get on their good side” converges with “not get one’s license to do business revoked” then there is not much daylight between that model and tech’s own. I am making this observation generally, on the basis of years of industry experience, rather than on the specific basis of any conversation that happened that week.
Financial professionals not directly employed by tech companies themselves shared this model, articulated it, and attempted to profit from it in a way which is entirely permissible under capitalism. Bellwether tech stocks (including those of industry participants) sold off during market highs for non-tech indexes, pricing in regulatory risk to these businesses.
This was noted by many non-political industry observers. The WSJ quoted an equity analyst as saying:
The bottom line is that the odds of legislative action on privacy, antitrust and [liability shield Section] 230 just went up significantly.
Investment banks get market color on recorded lines. In tech we get it in DMs from people we’ve worked with before and will again. It flows up to decisionmakers when it needs to. Much color is tweets being pasted into Slack.
This is not limited to times of national crisis. Speed is edge. As an illustrative example, regulators learned FTX had tried suborning a bank from the NYT, who learned it from an informed source in Tokyo, who developed a package of proof after reading a single document posted to Twitter. Or so this writer speculates in a curiously specific and consistent manner.
Now, putting these observations together:
Imagine a coordination game with two sides of a fence. Players have to pick either side of the fence. They may announce their decision at any time, and may change it until all players have announced a decision. Payoffs to this game decline the longer one waits. They are catastrophically negative if the game ends with one player alone on a side. The game has no winners ever and you can’t refuse to play.
This game has a “race to be second” dynamic, where any credible commitment to a move, or observed move, strongly encourages any player contemplating the same move to immediately announce it. Each additional player joining the block is a domino against players who have yet to announce.
The real-life situation reached rough equilibrium by January 10th.
Industry participants do not perceive themselves as having highly weighted the opinions of coalition participants during these few days. They were considered unimportant relative to other factors. Nor did industry participants broadly attempt to solicit input from coalition participants, in part because their responses were viewed as being trivially predictable. Further meetings during a crisis were considered a distracting waste of time.
Coalition members publicly and privately, along with many who had learned by imitation, immediately demanded everyone shut down everything. If he still had Netflix the next day it was not for want of trying.
Change the Terms issued a joint statement [archive] demanding an absolute Trump ban on January 6th itself using extraordinary language.
If platforms do not take immediate action to permanently remove Trump’s accounts, they will further share in the blame for additional white-supremacist violence that may unfold over the evening and in the remaining days before Trump’s term as president ends.
The House Financial Services Subcommittee on National Security, International Development and Monetary Policy held a hearing titled Dollars Against Democracy: Domestic Terrorist Financing in the Aftermath of Insurrection. SPLC’s Brooks again offered prepared testimony. The SPLC appears to ask Congress for new legislation establishing a BSA-style mandatory reporting regime, with penalties for non-compliance, across industry participants.
Verbatim quotes, bolding in original:
Government should require regular, mandatory reporting by technology service providers to document abuse of their systems including financial support of violence, harassment, and terrorism.This includes implementation of mandatory financial abuse reporting requirements for internet services operating in the United States, including social media services, infrastructure providers, banking institutions, cryptocurrency exchanges, crowdfunding sites, video streaming platforms, and the like.
and
[These companies] should be required to investigate and report the details of harms and abuse of their service. There should be … penalties applied to services that refuse these tracking and reporting responsibilities.
Given that this reporting regime is mandatory, on the face of it, if a respected civil rights organization makes a payment to an individual responsible for violence, harassment, and/or terrorism, facilitators would have an immediate reporting requirement. That seems to carry the risk of reporting on the actions of an NGO to a potentially hostile government. That government could be the current one or a future one, because governments have been known to keep written records and employ personnel who serve across generations.
Had the SPLC asked me for comment on this novel expansion of BSA-style enforcement mechanisms, I would have told them that the existing BSA enforcement apparatus routinely negatively impacts marginalized individuals the SPLC makes the center of their moral concern. Bits about Money has made this argument across many pieces and in depth for years, continuing on observations I had made during my time as a consumer advocate for individuals with banking and credit problems, dating to the mid-2000s.
Facebook announced that it would end its longstanding "newsworthiness exception” to content moderation rules. This was a concession to years of repeated public and private demands by CTT coalition members. These demands included the October 2019 letter co-signed by 46 organizations including several CTT coalition members.
This form of exception was called out in the CTT Terms and ending it was an avowed goal of the coalition.
CTT coalition members then pushed for another concession they desired.
Industry participants have characterized coalition members as being routinely undisciplined, verbally and in writing, in specifically nominating FEC-registered entity controlled accounts, including fundraising accounts, for termination. They claim this was a pattern of practice for several years. Bits about Money has reviewed multiple records suggestive of this pattern.
It is not straightforward to authenticate documents obtained through sources. More rigorous authentication often poses additional risk to sources.
On the other hand, sometimes documentary evidence of the pattern is available from the coalition directly. Common Cause maintains a WordPress site, and occasionally posts their target lists in public. [archive] WordPress is a complex and highly modular open source platform which you could use for a blog or e-discovery delivery service.
Bits about Money’s eclectic collection of coalition-authored communications unequivocally demonstrates a) multiple coalition members b) specifically directing account termination and/or continuous restriction c) against Trump-affiliated accounts d) for the express purpose of interdicting political fundraising and other activity e) with them subsequently fundraising in specific reliance upon these acts. We offer the published document in substantiation of claims a-d and the next section of this piece in substantiation of claim e.
Verbatim quotes from the document:
As you know, The Team Trump Facebook page is operated by Save America, a political action committee (“PAC”) controlled by Trump.
and
Allowing Team Trump to continue running political ads on Facebook is a significant loophole in Trump’s two-year suspension and provides a pathway for the former president to evade the ban. … Further, Team Trump is soliciting donations and inviting supporters to Trump rallies.
and
[We urge you to s]ubject the Team Trump account and any other account under Trump’s control, including any account of a political committee authorized and/or established by Trump pursuant to campaign finance law, to the same two year-ban as his Facebook and Instagram accounts.
No other accounts are specifically nominated in this document.
The document makes a token gesture that the principle is broader than the specific PAC whose fundraising activities it desires to be interdicted.
[We urge you to s]ubject any Facebook pages run by a political committee or other political entity authorized, established, financed, maintained or controlled by an individual to the same content moderation decisions as that individual’s Facebook account.
The Common Cause demand letter was co-signed by CTT coalition members Common Cause, CAP, Free Press, GPAHE, Media Justice, NHMC, and many other aligned 501c3 organizations. The published version of the demand letter is not signed by the SPLC.
Consider what level of operational discipline prevailed in the coalition, which employs many communications professionals and lawyers, to publish that document. Now imagine what individual coalition employees wrote with their thumbs. Do you picture excessive emoji, or prose that reads more Blackberry.
Coalition participants Free Press and Common Cause rented a mobile billboard to reiterate their demands. The mobile billboard was deployed to follow Facebook executives around Washington D.C. They tie this action to organizing to achieve a government investigation of Facebook.
Verbatim quotes from their press release [archive], titled Facebook Targeted by Mobile Billboard Circling Capitol Hill Demanding That Company Close the Trump Ad Loophole:
A mobile billboard demanding that Facebook ban Team Trump ads in accordance with its ongoing suspension of Donald’s [sic] Trump’s accounts will greet Facebook representatives following their Capitol Hill testimony today.
and
Sponsored by Free Press Action and Common Cause, the mobile billboard began its route
this morning and is continuing to circle the Federal Trade Commission, the White House,
Facebook headquarters and the U.S. Capitol, and will join the “Rally to Investigate Facebook”
We below reproduce Chris Cruz 8 Media Group’s photo of the mobile billboard, attached to the press release. The mobile billboard reads “Facebook must close Trump’s ad loophole” and “Nobody is above the rules.” We believe this reproduction is fair use for the purpose of reporting and commentary, but are happy to pay any reasonable fee for an unrestricted non-exclusive perpetual worldwide license across all media types currently existing or to be invented. Invoice to Kalzumeus Software, LLC please.

Free Press’s 2021 end of year communication [archive] to donors, signed by its co-CEOs, attempted to fundraise in part based on their participation in the Change the Terms coalition and in part based on the mobile billboard campaign to interdict PAC fundraising. The communication includes a photo of the billboard. All following quotes are from the document, and bolding is true to the original.
[W]e co-founded Change the Terms, a coalition that calls on the platforms to adopt model policies we developed to crack down on hateful content.
…
Our efforts have yielded numerous concrete changes. After years of pressure from Free Press and our allies, Twitter finally banned Trump[.]
…
Facebook initially suspended Trump “indefinitely” and later changed his suspension to a two-year ban. We’re now pushing the company to permanently ban Trump and to close a loophole that’s allowing a Trump PAC to fundraise and organize on his behalf.
The funding call to action, immediately above a donate button, was:
FUND THE FIGHT. Your generosity makes our work possible. Please give what you can today to make sure we have the resources we need to keep fighting for equitable media policies that improve people’s lives.
The communication included the following disclaimer, directly under the donation call-to-action. It was italicized.
Free Press and Free Press Action are nonpartisan organizations fighting for your rights to connect and communicate. Free Press and Free Press Action do not support or oppose any candidate for public office.
Meetings between industry participants and coalition participants decline from being a regular practice to occasional and ad hoc. This is according to several industry participants in past meetings. The Change the Terms social media presences, which had posted regularly from 2018 through 2021, substantially cease operations. Their last Medium post was in May 2022.
CTT coalition member GPAHE released a statement [archive] about Facebook and Trump on January 25th, 2023. The Change the Terms coalition retweeted it, in one of their final Twitter posts, and the final one naming Trump.
The most striking difference from the CTT coalition’s past several years of public and private statements: this is, conspicuously, carefully worded.
There was no urging, calling upon, demanding, etc in this public statement. It was comparatively disciplined in only describing Facebook’s decision and their analysis of it, and letting a rhetorical question hang in the air.
If that’s not enough for Facebook to continue to ban him, then what is?
The Change the Terms coalition website remains up, but it is difficult to say whether any members maintained their longstanding non-partisan interest in shaping industry policy via pressure campaigns and then nominating targets for enforcement. Perhaps they achieved final victory over hate.
Or perhaps, since September 2021, they had learned operational discipline. The kind that chuckles at a proposal to chase executives around with mobile billboards demanding the interdiction of PAC fundraising, in a totally non-partisan fashion of course, and then doesn’t do that. Donor funds are best spent elsewhere.
In other news, Trump had filed his candidacy paperwork with the FEC in November 2022. He would go on to win the 2024 election.
[Update on May 8th, 2026: At the time of publication of this essay, Bits about Money was unaware that the coalition had written, on its own letterhead, a demand letter after Trump was a declared candidate. We would not have written this section in the fashion it is written had we been aware of that document. Our discovery of it caused us to do substantial follow-on reporting. Bits about Money regrets the error.]
Wiley Coyote Charities, an IRS-recognized 501c3 non-profit organization in a universe not too far from our own, has chased its hated nemesis for years. The orange road runner is tantalizingly close. Focused and untiring, perceiving himself close to ultimate victory, Wiley Coyote Charities salivates. This time, this time for sure, he will be sated. He will be free.
Wiley Coyote Charities speeds past a sign reading “Danger: Plausible Non-Partisanship Ends.” The only danger is to that blasted bird.
Wiley Coyote Charities is, to the appearance of observers of the race, now running over two miles of clear blue sky. He has not yet looked down. We know what will happen when he does. Blame the road runner all the way down.
As a former 501c3 CEO myself, I am aware of the requirements to maintain tax-exempt status. This is of paramount importance to charities. You can save yourself some legal bills quickly with the IRS's Restriction of Political Campaign Intervention by Section 501(c)(3) Tax-Exempt Organizations :
"Under the Internal Revenue Code, all section 501(c)(3) organizations are absolutely prohibited from directly or indirectly participating in, or intervening in, any political campaign on behalf of (or in opposition to) any candidate for elective public office. Contributions to political campaign funds or public statements of position (verbal or written) made on behalf of the organization in favor of or in opposition to any candidate for public office clearly violate the prohibition against political campaign activity. Violating this prohibition may result in denial or revocation of tax-exempt status and the imposition of certain excise taxes."
501c4 organizations have similar considerations. Consult your lawyer.
BAM mostly explains and analyzes financial infrastructure. The pipes work for everyone in every party, and for that thank God, plus the many people who go to work every day to make it happen.
A reader unfamiliar with years of issues will assume, picking one at random, that we are sympathetic to the then-current administration because we referenced an indictment. We say very similar things at substantial length every single time. Some pieces you may enjoy: The Bond Villain compliance strategy re: CZ, an extensive discussion in Debanking and Debunking of bank compliance failures enabling the FTX fraud, and our voluminous record on the function and tradeoffs of the BSA regime.
Bits about Money does not generally recommend particular providers of financial services, including of screening data products. As an editorial decision: we anti-recommend the SPLC blacklist. It is unfit for purpose in financial services and obviously so. We have no position as a publication as to whether it is valuable for other uses.
To the extent I personally have policy preferences, I prefer the orderly administration of law. Any law we would not be willing to enforce against a sympathetic lawbreaker, a friend, or an ally is a bad law. Until a bad law is changed, it is the law. I reject a legal realism, or legal cynicism, that says that power is the only law.
The Declaration of Independence and D.C. billboards agree: No one is above the rules. We have no kings in this country.
On the SPLC specifically, I don’t really specialize in charity effectiveness ratings, but so I am not accused of hiding the ball: I think they achieved a meaningful and historic victory in the cause of righteousness many years ago. They have dined well on that reputation for a very long time.
To those who think their mission remains critical and more intrinsically noble than simply the pursuit of political power for their favored coalition, I will say this. If the coyote has a noble mission on his back, he owes it to the mission to let the damned bird go, before he takes that mission off the cliff with him.
Just following up on my emails. Do I have the correct addresses? Emails to the team alias and your personal work accounts, formatted correctly, did not bounce; emails to incorrect guesses for the team alias did.
SPLC: I had asked you to deny that the email between the SPLC’s CEO and bank exists or dispute the accuracy of the excerpt in the indictment, and asked you to comment on whether the Change the Terms coalition you co-founded had specifically nominated accounts for negative actions. I still welcome a denial or comment from you on any matter, like whether it is fair to characterize Change the Terms as the SPLC’s concerted coalition to interrupt the fundraising of political opponents.
Common Cause: I asked you to comment on whether you have ever nominated the account of an FEC-registered entity for negative decisioning, and told you I had written evidence of you doing so on at least one occasion. I welcome your future comment, perhaps on when you started that practice and when or whether you have ceased. We could compare notes.
Email is my preference, but since the SPLC specifically is well-resourced to pursue the other way to deliver a response if it desires, I’ll save everyone 6 billable minutes: tell them “to Kalzumeus Software, LLC’s registered agent.” The Internet and I will read it attentively.
To the as-yet uncontacted coalition members, that meeting can be an email: “How about ‘We categorically deny ever directing any company to interfere with fundraising of a political opponent.’ ?” “Approved. Next topic?” Unless you doubt that is true, in which case, book the non-partisan conference room for workshopping the language.
Don’t worry, I am a reasonable professional. Most journalists haven’t worked in a comms department. I have, and so gave all parties contacted several business days to answer very simple questions.
Your employer is profoundly opposed to you sending confidential information to external parties, even a fellow geek. The incremental value of evidence to me is far lower than risk to you.
Audit logs exist, including for searches and document accesses.
Remember the front page test. If you write it down, you could read it in the NYT. Or HN. So don’t write down anything you wouldn’t want published next to your name for forever.
2026-02-07 01:13:22
There was recently an attempt by an independent journalist to expose fraud in a Minnesota social program. It was deeply frustrating; the journalist had notably poor epistemic standards, which secondary media seized upon to dismiss their result.
The class-based sniffing almost invariably noted that prestige media had already reported stories which rhymed with the core allegation, while sometimes implying that makes the allegations less likely to be true, through a logical pathway which is mysterious to me.
The journalism went quite viral anyway, in part because of sensationalized framing, in part because of signal boosting by an aligned media ecosystem and aligned politicians, and in part because the journalism develops one bit of evidence that has a viscerality that paperwork dives often lack: these purported childcare operations routinely have no children in them.
Fraud has become quite politicized in the United States the last few years. We had a poorly-calibrated federal initiative led by a charismatic tech entrepreneur which believed it would unearth trillions of dollars of fraud that focused substantial effort on large programs which are comparatively fraud-resistant. Across the aisle, we have reflexive dismissal that fraud happens in social programs, which functions as air cover for scaled criminal operations which loot many varied social programs [0] and are sometimes run out of geopolitical adversaries of the U.S. including by ambiguously-retired members of their clandestine services.
I worked in the financial industry for a few years. We do not have the luxury of pretending that fraud is something invented by our rivals to besmirch our good name. It hits the P&L every quarter and will eat you alive if you’re not at least minimally competent in dealing with it. Conversely, it is well-understood in industry that the optimal amount of fraud is not zero.
The financial industry has paid at least tens of billions of dollars in tuition here. Overwhelmingly, one learns about fraud in it through an apprenticeship model, with different firms having different internal levels of understanding on the shape of the elephant. The industrial organization presumes small numbers of people architecting anti-fraud systems and relatively larger numbers of investigators and analysts operating those systems on a day-to-day basis.
There does exist some informal knowledge sharing between firms. If you work in payments, try getting invited to the Chatham House rule sessions held by… oh yeah, can’t say. Despite that social technology being originally developed for the benefit of government and press actors, it is my general impression that U.S. benefits programs don’t yet see themselves as sufficiently yoked by adversarial attention to benefit from their own Chatham House series. Perhaps that should change.
And so, for the benefit of fraud investigators with badges, press cards, or GoPros, some observations from a community of practice with an extensive (and mostly nonpublic) body of work. But first a tiny bit of throat clearing.
Minnesota has suffered a decade-long campaign of industrial-scale fraud against several social programs. This is beyond intellectually serious dispute. The 2019 report from the Office of the Legislative Auditor (a non-partisan government body) makes for gripping reading. The scale of fraud documented and separately alleged in it staggers the imagination: the state’s own investigators believed that, over the past several years, greater than fifty percent of all reimbursements to daycare centers were fraudulent. (Separate officials took the… novel position that they were only required to recognize fraud had happened after securing a criminal conviction for it. Since they had only secured a few criminal convictions, there was no way that fraud was that high. Asked to put a number on it, repeatedly, they declined.)
The investigators allege repeatedly visiting daycare centers which did not, factually, have children physically present at the facility despite reimbursement paperwork identifying specific children being present at that specific time. The investigators demonstrated these lies on timestamped video, and perhaps in another life would have been YouTube stars.
Our social class is intensely averse to straightforwardly recounting these facts, partly due to political valence and partly due to this particular fraud being dominantly conducted within a community which codes as disadvantaged in the U.S. sociopolitical context.
Fraudsters are liars and will cheerfully mouth any words they believe will absolve them of their crimes. If an accusation of racism gets one a free pass to steal hundreds of millions of dollars, they will speciously sue you alleging racial discrimination. That empirically worked in Minnesota. The OLA takes explicit notice of this multiple times, a coordinator for the fraud operation is on record explicitly explaining the strategic logic of accusations of racism, and a judge was even moved to make an extraordinary statement to clarify that the bad-faith lawsuit alleging racism did not achieve success through the formal judicial process but rather through the voluntary compliance of governmental actors shamed by its allegations.
(As a sidenote: one has to be able to hold two thoughts simultaneously about fraudulent operations. They can be sophisticated with respect to exploiting sociopolitical cleavages in their targets while also being comically inept at faking evidence elsewhere, such as having a single person write dozens of adjacent rows in a sign-in sheet. This routinely surprises observers and it should not surprise them. The financial industry also has a division of labor in it. The person architecting the fraud department’s standard processes is well-paid, well-educated, and routinely brings crossdisciplinary expertise to bear. A Fraud Analyst I, on the other hand, bears a lot of similarity to a call center employee in terms of compensation, education, and permitted amounts of agency.)
In the immediate wake of the independent journalist’s report, the great and the good rallied around the organizations he accused. Of course it was natural that journalists wouldn’t get immediate access to children if they asked. Of course there was a certain amount of informality in the sector. Of course, as the New York Times very carefully wordsmithed recently:
Minnesota officials said in early January that the state conducted compliance checks at nine child-care centers after Mr. Shirley posted his video and found them “operating as expected,” although it had “ongoing investigations” at four of them. One of the centers, which Mr. Shirley singled out because it misspelled the word “Learning” on its sign, has since voluntarily closed.
An inattentive reader might conclude from this paragraph that the Times disputes Shirley’s reporting.
To the extent that Bits about Money has an editorial line on that controversy, it is this: if you fish in a pond known to have 50% blue fish, and pull out nine fish, you will appear to be a savant-like catcher of blue fish, and people claiming that it is unlikely you have identified a blue fish will swiftly be made to look like fools. But the interesting bit of the observation is, almost entirely, the base rate of the pond. And I think journalism and civil society should do some genuine soul-searching on how we knew—knew—the state of that pond, but didn’t consider it particularly important or newsworthy until someone started fishing on camera.
But this is not a publication about particular ponds. It is a publication about getting better at fishing.
The best non-fiction work on fraud is Dan Davies’ Lying for Money. In it, you’ll find replete examples of something well-known to fraud investigators: the dominant next adventure for a former fraudster is… opening up a new fraud. And therefore, if you want to identify a ridiculously-high-hit-rate list of frauds in round N+1 of a game, a so-easy-its-practically-cheating way to do so is to look at what known fraudsters from round N are doing today.
There is a genuine difference in the culture and epistemology of the financial industry versus the government of the United States here. In the financial industry, we keep blacklists and getting a second chance after obvious misbehavior is intentionally non-trivial. This runs against deeply felt values of civil servants. An accusation is not a conviction, and absent clear authority to impose consequences in a new program, an actor convicted at enormous societal cost emerges to a new program officer as tabula rasa, equal in moral worth to any randomly chosen citizen.
I will not argue that Mastercard has better moral intuitions than the Founding Fathers. I would, however, happily suggest that the government not assume that the Constitution contains emanating penumbras obligating it to be repeatedly taken advantage of by the same people in the same fashion. We are not forbidden object permanence.
Minnesota raided the Sunshine Child Care Center in 2022 on suspicion of overbilling. No charges were brought, in what investigators imply was less an exoneration and more an inter-departmental fumble. That operation was owned by one Fowsiya Hassan. A separate childcare center owned by Fowsiya Hassan was featured on YouTube recently. This follows on $1.5 million of funds received through Feeding Our Future, a scaled fraud operation which has generated over 70 indictments, 5 criminal convictions, and 50 guilty pleas. What a set of coincidences. Perhaps Hassan has, as she has alleged in a lawsuit, been a frequent target of racially-motivated government investigations into a successful serial entrepreneur in the childcare field.
Much of the intellectual energy in policy circles about fraud is aimed at retail-level fraud by individual beneficiaries. Most fraud, like most scaled property crime, is actually the result of a business process.
This is an elementary fact of capitalism. It is deeply disconcerting to find every benefits program independently rediscovers it a decade too late to do anything about it. Most bread is not baked by amateurs in their kitchens. It comes from a bakery which exists to bake bread and hires specialists in baking bread and then supports them with capital-intensive built infrastructure.
Fraud develops a supply chain. Some elements in the supply chain are dual-use; the bad guys use Excel for the same reason every business uses Excel. Some elements in the supply chain, though, are specialized infrastructure with no or de minimis legitimate purpose. Those elements can be profiled.
I worked at Stripe for several years and am currently an advisor there. Stripe does not endorse what I write in my personal spaces. In its own spaces, Stripe has discussed being able to follow fraudulent operations in sufficient detail to determine when the operators went to lunch.
Fraudsters share specialists quite frequently. They use the same incorporation agents, the same mail services, the same CPAs, the same lawyers, etc.
You can make the same observation about many communities of practice. It is a non-coincidence that many tech startups are at 548 Market Street in San Francisco. 548 Market Street is not the world’s hippest coworking space. It is the address for EarthClassMail in SF. There are many P.O. box providers in the world; many geeks with taste reach for ECM. (Bits about Money is legally required to maintain a postal address and, if you were ever to send it a physical letter, that would also end up in the hands of an EarthClassMail employee.)
Elsewhere in the world, there exist P.O. box providers whose customers statistically include fewer AI labs and more frauds. One imagines the specialist-in-fraud at the storefront, picking up the day’s take from fifteen separate boxes.
Elementary work graphing supporting infrastructure, even on something as unsophisticated as butcher paper, frequently unravels fraud networks. Data science has any number of more sophisticated approaches. Jetson Leder-Luis, an academic who now routinely works with the government, has previously discussed some approaches which work based on widely commercially available data sources.
There is an emerging defender’s advantage here in the age of LLMs, since exploratory work in visualizing and walking network graphs is getting much cheaper. You no longer need to buy Palantir and engage a “forward-deployed engineer” to cluster IP addresses. A non-technical fraud investigator could get an LLM to do that while eating at Chipotle, and the lunch would cost more.
This democratization of capabilities is relevant to journalists, formal and otherwise, and also to governments. RFPs and software contracting once de facto mandated a multi-year lead time to do an automated network analysis if an analyst thought perhaps their program might need one. Now that is an afternoon’s work, if we allow ourselves to do it. We should.
As mentioned, there is enormous visceral distaste for the conclusion that a particular fraud ring operates within a particular community. This is quite common. You should expect to find circumstances which rhyme with it when conducting effective fraud investigations. You should not abandon fraud investigation when you chance upon this.
People assume a level of ethical fraughtness here which is not warranted. You would, if doing ethnographic work on perfectly legitimate businesses across industries, routinely discover ethnic concentration rather than population-level representation everywhere you looked. The Patels run the motels. One doesn’t need to adopt grand theories about how certain groups are predisposed to becoming pharmacists or startup employees or line cooks; simple microeconomic reasoning explains reality easily. Firms hire the people they already know, like, and trust. That will routinely include friends and family, who are going to be much more like the founding team than they are like randomly drawn members of the population. This is the default outcome.
Fraudsters do have one structural factor here. Everyone wants to trust their coworkers. Fraudsters need to trust their coworkers will be loyal even upon threat of prison time. That necessarily selects for tighter bonds than the typical workplace. Madoff was a family affair, SBF was in an on-again off-again romantic relationship with a chief lieutenant, and neither of those facts is accidental or incidental.
That’s the other ethical dimension of being other-than-blind to concentration: so-called affinity frauds do not merely recruit fraudsters from affinity groups. They recruit victims from affinity groups. Madoff mobilized the social infrastructure of the Jewish community in New York and Palm Beach to find his marks. Community members certainly did not intend their charitable foundations to be looted by a fraudster. It was an emergent consequence of trust networks.
This also happens to “chosen” communities. FTX was, in material part, an affinity fraud against effective altruists, who are not a religion or ethnic group as traditionally construed.
And so when the great and the good turn a blind eye towards abuses because the perpetrators share an uncomfortable common factor, they are often simultaneously turning a blind eye towards abuses of a community whose interests they purport to champion.
As covered extensively in Lying for Money, the necessary fundamental conceit of a fraud is growth in a business that doesn’t happen in the real world. “Every lie told incurs a debt to the truth, and one day, that debt will be paid”, to quote the excellent drama mini-series Chernobyl. Fraudsters forestall that day of reckoning by telling a bigger lie, increasing the debt, which (mostly as a side effect) alleges that they’re growing much faster than most of your legitimate portfolio. Happily, many businesses have figured out how to keep track of fast-growing customers. Tracking rocketships doesn’t require rocket science.
Sort-by-growth-rate-descending on new accounts will turn up a lot of interesting observations about the world. One is that Fortune 500 companies sometimes open new accounts, and you probably don’t need to open a fraud investigation file in that case. Another is that some people claim to be feeding millions of meals to a community of tens of thousands of people, beginning from a standing start, and growing local social services at a rate which an Uber Eats city manager would not expect to achieve in the wildest dreams of their go-to-market plan.
Feeding Our Future had a CAGR of 578% sustained for 2 years. Uber, during their meteoric growth period in core rideshare services, had an average CAGR of 226%. Their best year was 369%. But, if you asked in Minneapolis in 2021, you’d quickly find someone who had been in an Uber, but fail to find anyone who ate courtesy of Feeding Our Future. So curious, given that they were drubbing one of the fastest growing companies in history on growth rate.
Investigators in Minnesota were ringing the alarm bells for years about implausibly fast growth in Feeding Our Future’s reimbursement requests, including at new facilities. Feeding Our Future felt it was maxed out on the fraud it could conduct at existing sites, and expanded voraciously, including (most prominently) enrolling numerous restaurants as “feeding sites.” They then copy/pasted the usual playbook and requested reimbursement for implausible volumes at those sites, paying kickbacks to many participants. This then required growing the fraud, which… you get the general idea. We could have gotten off the bus at many points, and I suppose that is at some level a question of political will.
The highest growth rates in the economy generally are newer fields (you basically can’t sustain the alternative). This doesn’t imply that those fields are fraudulent, but they will tend to disproportionately attract frauds. The defenders in those fields have not yet paid their tuition to the School of Hard Knocks, and so attackers target the weaker systems. The higher growth rates of legitimate businesses function as protective cover for high stated growth rates of illegitimate businesses; a CAGR of 1,000% looks implausible for a restaurant but barely-meets-expectations for an AI software shop.
And, not to put too fine a point on it, many people are invested, literally and metaphorically, in whatever today’s new hotness is. People who could not secure an allocation in the more legitimate ends of it will sometimes find themselves adversarially selected by less salubrious actors. This will read to those people as a justly earned success. They might even have their marketing department write up their victimization as an indisputable success.
And so, if you’re a defender who has many different lines of business and has limited resources (or political will), where should you deploy those resources? Should you place your bets on e.g. Social Security, a multi-trillion dollar program whose primary source of growth is fun to conjure but then requires 70 years of seasoning? Or should you place them on the Paycheck Protection Program, or pandemic-era unemployment insurance, or genetic testing, or non-emergency medical transportation? Despite those being smaller line items, they probably have more juice worth squeezing, and the fraud is more easily detectable. Just look.
Bits about Money has extensively covered anti-moneylaundering and Know Your Customer regulations and I won’t rehash those regimes here. A bit of tacit knowledge in the financial industry: some actors in the set “broadly considered trustworthy” are more worthy of trust than others… and some are less.
We are generally discreet about writing this down in as many words. But, as an analogy, cross-national regulatory bodies require that financial institutions maintain a list of high-risk jurisdictions to do business in. You are generally required to do enhanced due diligence on customers/activities/etc touching the high-risk list.
If you are particularly competent, and there are plusses and minuses to being competent in detecting fraud (you will not be the most popular person in the firm at bonus time; that goes to the folks who sold the high-growth accounts), you might have the analogous list of U.S. financial institutions which are not entirely fronts for the bad guys.
If one hypothetically has that list, that’s one more signal you can use in evaluating any particular account, and a one-stop shop for developing a list of accounts to look into. It would be uncouth of me to name an extant bank that has poor controls, but for a general example of the flavor, see my (scathing) commentary on Silvergate’s AML and KYC program. Without using any proprietary information, I predict confidently that Silvergate banked many more multi-billion dollar frauds as a percentage of its customer base than almost any of the U.S.’s 4,500 banks. (Trivial substantiation: divide FTXes-banked by total-count-of-customers.)
One might, if one has never seen the list, wonder whether it is simply proxying for something the financial industry is definitely not allowed to proxy for. One of the first things you learn as a data analyst is zip codes are extremely probative and you are absolutely not allowed to use them. The American system remembers the experience of redlining and has forbidden the financial industry from ever doing it again; the industry mostly respects that. But good news: institutions with weak controls environments are not, in fact, simply a proxy for “Who banks socially disadvantaged people?” There are many financial institutions that have that as an explicit business model. Some of them are good at their jobs. Some, less so, and the fraudsters know it.
This sometimes happens with the knowing connivance of the financial institution and/or their staff. For much more on that, see histories of the savings and loan crisis, or the Lying for Money chapter on control frauds. But more commonly it is simply a community of practice developing organic knowledge about who is just very easy to get an account with. You need accounts, as a business. As a fraudulent business, which intends to cycle through accounts and identities at a much higher rate than baseline, you would prefer to do business with a bank which will not detect that malfeasance.
And so you will disproportionately end up banked, with many of your buddies, at the least attentive place still capable of getting a license. And so an agency, trying to find a fraudulent network, might want to look at fraud-cases-by-routing-number and then start making some judgment calls.
One of the reasons the government has deputized the financial industry is it is good at keeping spreadsheets and quickly responds to requests for them. Perhaps the government should call up a few of their deputies and say “So, not alleging anything here, but we think you might have a list, carefully maintained by your fraud department for your own purposes. We want to see the list. It would be pro-social of you to give us a copy of it.”
There is a thriving market in identities to be used in fraud. This is because bad actors prefer not putting their own names on paper trails certain to become evidence, because they frequently “burn” themselves early in their careers, and because institutions have cottoned onto the wisdom of collecting lists of ultimate beneficiaries.
Sometimes this is a social process, conducted at e.g. the dinner table. Sometimes the market is explicitly a market. Jetson recounted that, having exhausted the supply of patients needing dialysis who could plausibly need ambulance services, frauds began bribing potential patients, first with donuts and then with cash. This is extremely common. In Minnesota, parents were recruited to childcare providers with the promise of cash kickbacks or (a detail we’ll return to in a moment) fictitious paperworked no-show jobs, sometimes at substantially fictitious companies.
Fraudsters sometimes exercise some level of operational discipline in their communications. The bad guys have also seen The Wire; they know Stringer Bell’s dictum on the wisdom of keeping notes on a criminal conspiracy. However, the population of people willing to be named in a federal indictment over $200 necessarily selects preferentially for individuals who are not experts at operational security. They will sometimes organize recruitment very openly, using the same channels you use for recruiting at any other time: open Facebook groups, Reddit threads, and similar. They will film TikTok videos flashing their ill-gotten gains, and explaining steps in order for how you, too, can get paid.
As a fraud investigator, you are allowed and encouraged to read Facebook at work.
Now, knowing that there exists the frequent epiphenomenon where fraudsters recruit strawmen to use their identities to qualify for payments: suppose that you have an entirely new enterprise whose first customers are individuals A, B, C, and D. You know, from past records, that A, B, C, and D have all been customers of an organization which you now know, positively, was a fraudulent actor. You might infer from this that A, B, C, and D might have sold their identities once, but you probably don’t have sufficient information to convict them in a court of law of that. (It is of course possible that they are simply unsophisticated, or that bad actors obtained their information without their knowledge, for example by misappropriating a client list from a previous corporate entity they happened to own/work for/etc.)
But do you have enough information to take a more-detailed-than-usual look at this totally new enterprise? I think you do.
We have choices, as the defender, in what levels of evidence we require to enter the circle of trust, what our epistemological standards are, and how much evidence we require to forcibly exit someone from the circle of trust.
A detail from the Minnesota cases is that these burdens are asymmetric, in a way which disadvantages the defender (all of us). That decision is a choice and we should make better choices.
For example, the primary evidence of a child attending a day-care was a handwritten sign-in sheet of minimal probative value. Prosecutors referred to them as “almost comical” and “useless.” They were routinely fraudulently filled out by a 17 year old “signing” for dozens of parents sequentially in the same handwriting, excepting cases where they were simply empty.
To refute this “evidence”, the state forced itself to do weeks of stakeouts, producing hundreds of hours of video recording, after which it laboriously reconstructed exact counts of children seen entering/exiting a facility, compared it with the billing records, and then invoiced the centers only for proven overbilling.
On general industry knowledge, if you are selected for examination in e.g. your credit card processing account, and your submission of evidence is “Oh yeah, those transactions are ones we customarily paperwork with a 17 year old committing obvious fraud”, your account will be swiftly closed. The financial institution doesn’t have to reach a conclusion about every dollar which has ever flowed through your account. What actual purpose would there be in shutting the barn door after the horse has left? The only interesting question is what you’ll be doing tomorrow, and clearly what you intend to do tomorrow is fraud.
We can architect the asymmetry in the other fashion: legitimate businesses will customarily, as a fact of their operations, put enormous effort into creating visible effects in the world which are trivial to check. In technologist circles this is sometimes called a “proof of work” function.
Once upon a time, a team of fraud analysts asked how they could possibly determine frauds from non-frauds without having extensive industry knowledge about every possible commercializable human activity. I suggested that a good first pass was “Just ask the correspondent for a quick video, shot on their cell phone, of their workspace.”
That is minimally invasive for the business owner, generates a huge amount of signal (including that which can be correlated across accounts), and can be usefully adjudicated by non-specialists in a minute. No multi-month stakeout of their storefront is required. Of course you can convincingly fake a video of working in, say, a machine shop, but fraudsters maintaining spreadsheet row 87 about the machine shop will find that difficult to juggle with all the other required lies in their backlog. Actual machine shops, meanwhile, include people, which means they include functional cell phone cameras at no additional cost to anyone.
You can also get some signal from who can trivially produce a video and who needs a week of advance notice to find a cell phone to record those machines that were absolutely milling aluminum last week.
Fundamentally, we have a choice about where we put our investments in defanging fraud, and we should stop choosing to lose.
So-called “pay-and-chase”, where we put the burden on the government to disallow payments for violations retrospectively, has been enormously expensive and ineffective. Civil liability bounces off of exists-only-to-defraud LLC. Criminal prosecutions, among the most expensive kinds of intervention the government is capable of doing short of kinetic war, result in only a ~20% reduction in fraudulent behavior. Rearchitecting the process to require prior authorization resulted in an “immediate and permanent” 68% reduction. (I commend to you this research on Medicare fraud regarding dialysis transport. And yes, the team did some interesting work to distinguish fraudulent from legitimate usage of the program. Non-emergency transport for dialysis specifically had exploded in reimbursements—see Figure 1— not because American kidneys suddenly got worse but because fraudsters adversarially targeted an identified weakness in Medicare.)
Attackers carefully respond to signals they think they are being sent from defenders. A lawyer for some of the Minnesota defendants, Ryan Pacyga, was quoted by the New York Times as saying that his clients understood Minnesota to tacitly allow their actions.
> No one was doing anything about the red flags. … It was like someone was stealing money from the cookie jar and they kept refilling it.
Don’t be the defender who sends that message. It will not work out well for you or your program.
Most frauds have rich external lives, with a soaring narrative of how deserving people are getting valuable services (and/or getting rich for being right and early regarding e.g. crypto asset cross-margining). They tend to be distinctly underpaperworked internally, partly because a synonym for “paperwork” is “evidence” and partly because… most frauds aren’t really that sophisticated, when it comes down to it. There is a true number; lie about it; done.
Like many time-pressed entrepreneurs busy talking to potential customers, fraudsters put the minimal amount of time necessary into bookkeeping and even less than that into paperworking epiphenomena of their frauds. One example of epiphenomena is sometimes the beneficiaries need their own paperwork. A legitimate mortgage company employs sales reps and a backoffice to help unsophisticated customers successfully get several hundred pages of paperwork together to sell a mortgage. Frauds… mostly don’t do that.
And so, if you have e.g. a statutory requirement that a beneficiary be employed to access services, a fraudster might say “Don’t worry about it!” They’ll just assert that you are an employee at a cleaning company. Perhaps they might even go as far as payrolling you as an employee of a cleaning company. This kills two birds with one stone, paying you your kickback while also generating the paystub they need you to have to qualify for the government reimbursement. (This happened, per the OLA’s reports summarizing the results of many investigations, in Minnesota.)
But fraudsters don’t actually operate cleaning companies even in those cases where they do operate daycares.
Cleaning companies are legitimate businesses, in the main, and working for one is an honest occupation. And so a fraud investigator should feel no chagrin at calling a cleaning company in the phone book and asking for a quote. A cleaning company which expresses complete befuddlement that someone could ask for a quote is providing, ahem, evidence in a direction.
(I have to note, as someone who pays to send children to a private school, that there is replete evidence that the school is accepting new children, knocking on the door and asking will quickly result in being given a brochure, and there are scheduled open houses and similar. I can imagine a gratuitously mismanaged educational establishment which does none of these things, and I can imagine an educational establishment which makes a lot of money, but I have trouble holding both thoughts in my head at the same time.)
The core frauds are sometimes hardened, to an attenuated degree. The peripheral frauds collapse under even a glance. Architect processes to require more signals regarding the periphery, then architect a system which takes at least a cursory look at the periphery. You will trivially catch frauds.
If you’re worried about exposing the exact signal that you are using, costing utility of it in the future, you can use this as a “parallel construction” engine. Develop leads for investigation using the non-public signal, pull the core records as a matter of routine, find the discrepancies that all frauds leave in their core records, and then put those in the indictment. Ask your friendly neighborhood lawyer if that passes muster or if you need to add a sentence rhyming with “was selected for a routine audit on the basis of information available to the department.”
We have discussed some heuristics [1] for identifying fraud. The financial industry still makes material use of heuristics, but a heuristic is a compression of the real world. It will sometimes lose fidelity to the world. It will frequently, by design, be legible to the adversary.
The defender has one advantage the attacker cannot ever replicate: data at scale. It knows what legitimate use looks like because it has all the messy, contradictory, varying quality, typos-and-all data which legitimate businesses in the real world constantly throw off. You cannot duplicate all of the shadows on the wall of Plato’s cave without first duplicating the entire world. Fraudsters, even quite talented ones, can’t do that.
There are any number of techniques for machine learning in anti-fraud; Emily Sands has previously discussed some with me. An important subset of the field can adapt in real-time or close to it to changes in adversary (or legitimate!) behavior. For example, covid surprised the fraudsters at the same time as it surprised every supermarket in the country, but the ex-post actions of the fraudsters and the supermarkets were very different. Revenue went up for both, but only one group actually runs a supermarket. And so by ingesting and constantly analyzing data from all users, including retrospective annotation of which users you’ve identified to be frauds, you get better and earlier signals on which users are likely fraudulent and which are likely not.
This can inform outright interdiction or the investigate-then-punish loop that we ordinarily expect from government. It can also inform less consequential, easier-to-reverse interventions. For example, rather than putting all users immediately through the highest-possible-ceremony process for application, you can let most users do a lower-burden process, saving the higher levels of scrutiny for those which signal greater likelihood of being fraudulent. Or you can default to approving more applicants and reserve more of your investigatory budget for post-approval review, with this being equivalently costly by using better tasking of those reviews versus random allocation. Pay-and-chase becomes more palatable if it is not pay-and-pay-and-pay-and-pay-and-chase and more pay-until-we-decide-to-chase-but-stop-payments-at-that-decision-not-after-the-catching.
Machine learning isn’t simply useful from a perspective of decreasing fraud. The history of regulation of benefits programs is the history of too-late, too-harsh overcorrection to notorious abuses. Much of what advocates find most maddening and Kafkaesque about eligibility criteria and application processes was voted on by a legislature but bears the signature of a fraudster with a novel idea.
With a good machine learning practice, you can increase data ingested but decrease the burdensome formal application/etc requirements. This is in no small part because those data points are less probative (they are under the direct control of the attacker and announce that they will be scrutinized). But it bears a dividend: if you better control fraud, and can successfully demonstrate that to the public and legislators, you can decrease application burden and perhaps even widen eligibility criteria. Those are both in the direct interests of potential marginal beneficiaries.
A political commentator might focus more on the optics here than on the substance, because that is so frequently where the point of actual leverage is in politics. But the substantive reality of fraud losses matters. It is much easier to tell the story of fraud in benefits programs being rare, opposed by all right-thinking people, and swiftly sanctioned when that story is not an obvious lie.
You can read Lying for Money or other histories of frauds for more detail on the texture, but in the main, a dedicated fraudulent enterprise is created, is seasoned for a while before crossing the rubicon, has a period of increasing brazenness, is detected, is closed, and then is resurrected when the fraudster gets the band back together from round N+1.
We can intervene against the lifecycle model if we understand it. This begins with not defaulting to the understanding of investigators that frauds are isolated incidents by disparate individual actors. Those have been known to happen, but frauds are, by total damage, dominated by repeatable business models perpetrated by professional specialized bad actors. We should study them like we study other successful entrepreneurs, and then not invest in them.
One actionable insight from the lifecycle model: because the fraudster intends to be in business multiple times in their life, we should track the person-to-business mapping much more closely than we have historically. As Lying for Money says, if you’re an accountant and willing to go to prison, and you do not get rich via fraud… well, you are very bad at your job. That’s on you. When we give you repeated chances to do it, that’s on us.
One might think that the simplest imaginable reform is passing some sort of beneficial ownership regulation to unroll complex corporate structures designed to obscure who is actually puppeting Totally Not A Fraud, LLC. But the simplest imaginable reform is probably just actually reading corporate filings that already exist and are public. Again, most fraudsters are not the hypersophisticated Moriarties of the popular imagination. The Minnesota fraudsters frequently did not even bother with fig leaves. While they did find some nominee directors in some cases, many of the convicted operated their companies in their own names, with no complicated structuring at all. Sometimes multiple times, consecutively, after the previous entities had worn out their welcome with Minnesota.
The Fed should not be surprised when the bad guys buy a bank when buying a bank requires an extended permission-seeking process and the bad guy’s corporate records, dutifully recorded by Maryland (entity D20033544), are signed by a notorious bagman. In the Fed’s defense, the bagman lied to them about his intentions, which was outside of their world model. (Pip pip to the New York Times for figuring that out before the Fed did. That is, sadly, not the usual way it works in financial journalism.)
Responsible actors in civil society have a mandate to aggressively detect and interdict fraud. If they do not, they cede the field to irresponsible demagogues. They will not be careful in their conclusions. They will not be gentle in their proposals. They will not carefully weigh consequences upon the innocent. But they will be telling a truth that the great and the good are not.
The public will believe them, because the public believes its lying eyes.
[0] In a thing you will see frequently in fraud investigations, early detection of anomalies does not necessarily imply successful identification of the underlying fraudulent enterprise. A teacher was scandalized that a third of their students are using AI to write papers. Those “students” are identities puppeted by a criminal organization to siphon federal funding out of community colleges towards accounts controlled by the criminals. (I award myself one cookie for correctly predicting this.)
[1] A heuristic, in industry parlance, is a hard-coded rule or set of rules as opposed to a system which automatically adapts to changes in the underlying data. Compare the difference between “You are less likely to default on loans if you own versus renting”, which is absolutely demonstrable in aggregate data, versus “You are less likely to default on loans at 780 FICO versus 540 FICO.” For a variety of reasons, the culture that is legislators sees the problem with having one heuristic, which will obviously not come to the correct conclusion all of the time. It corrects for this issue by having several hundred pages of heuristics. Just one more heuristic, man, and we’ll have completely anticipated all the complexity of the world.
Heuristics are wonderful things! They’re cheap to adjudicate, easy to explain, and can be understood by lawyers, even the kind who have ascended from the practice of law to the writing of it. Happily, machine learning systems can have all of these properties if you make them priorities.
2026-01-08 05:12:19

Programming note: Happy New Year! Bits about Money is made possible—and freely accessible to all—by the generous support of professionals who find it useful. If you’re one of them, thank you—and consider purchasing a membership.
The U.S. is often maligned as being customer-hostile compared to other comparable nations, particularly those in Europe. One striking counterexample is that the government, by regulation, outsources to the financial industry an effective, virtually comprehensive, and extremely costly consumer protection apparatus covering a huge swath of the economy. It does this by strictly regulating the usage of what were once called “electronic” payment methods, which you now just call “payment” methods, in Regulation E.
Reg E is not uniformly loved in the financial industry. In particular, there has been a concerted effort by banks to renegotiate the terms of it with respect to Zelle in particular. This is principally because Zelle has been anomalously expensive, as Reg E embeds a strong, intentionally bank-funded anti-fraud regime, but Zelle does not monetize sufficiently to pay for it.
And thus a history lesson, a primer, and an explanation of a live public policy controversy.
If you were to ask your friendly neighborhood reference librarian for Electronic Fund Transfers (Regulation E), 44 Fed. Reg. 18469 (Mar. 28, 1979), you might get back a document yellowed with age. Congress, in its infinite wisdom, intended the Electronic Funds Transfer Act to rein in what it saw as the downsides of automation of the finance industry, which was in full swing by this time.
Many electronic transactions might not issue paper receipts, and this would complicate he-said bank-said dispute resolution. So those were mandated. Customers might not realize transactions were happening when they didn’t have to physically pull out a checkbook for each one. Therefore, institutions were required to issue periodic statements, via a trustworthy scaled distribution system, paper delivered by the United States Postal Service. And electronic access devices—the magnetic-stripe cards, and keyfobs [0], and whatever the geeks dreamed up next—might be stolen from customers. And therefore the banks were mandated to be able to take reports of mislaid access devices, and there was a strict liability transfer, where any unauthorized use of a device was explicitly and intentionally laid at the foot of the financial institution.
Some of the concerns that were top of mind for lawmakers sound even more outlandish to us, today. Financial institutions can’t issue credit cards without receiving an “oral or written request” for the credit card. That sounds like “Why would you even need to clarify that, let alone legislate against it?!” unless you have the recent memory of Bank of America having the Post Office blanket a city with unsolicited credit cards then just waiting to see what happened. [1]
The staff who implemented Reg E and the industry advocates commenting on it devoted quite a bit of effort to timelines, informed by their impression of the cadence of life in a middle class American household and the capabilities of the Operations departments at financial institutions across the U.S.’s wide spectrum of size and sophistication. Two business days felt like a reasonable timeline after the theft of a card to let the financial institution know. They picked sixty business days from the postmark for discovering an unauthorized transaction in your periodic statements. That felt like a fair compromise between wanting to eventually give financial institutions some level of finality while still giving customers a reasonable buffer to account for holidays, vacation schedules, the time it takes a piece of mail to travel from New York City to Hawaii, and the reality that consumers, unlike banks, do not have teams paid to open and act upon mail.
And, very importantly for the future, Congress decided that unsophisticated Americans might be conned into using these newfangled electronic devices in ways that might cost them money, and this was unacceptable. Fraudulent use of an electronic fund transfer mechanism was considered an error as grave as the financial institution simply making up transactions. It had the same remedy: the financial institution corrects their bug at their cost.
“Unauthorized electronic fund transfer” means an electronic fund transfer from a consumer's account initiated by a person other than the consumer without actual authority to initiate the transfer and from which the consumer receives no benefit.
Reg E provided for two caps on consumer liability for unauthorized electronic fund transfer: $50 in the case of timely notice to the financial institution, as sort of a deductible (Congress didn’t want to encourage moral hazard), and $500 for those customers who didn’t organize themselves sufficiently. Above those thresholds, it was the bank’s problem.
Reg E also establishes some procedural rights: an obligation for institutions to investigate claims of unauthorized funds transfers (among other errors—Congress was quite aware that banks frequently made math and recordkeeping mistakes), to provisionally credit customers during those investigations, strict timelines for the financial institutions, and the presumptive burden of proof.
In this privately-administered court system, the bank is the prosecutor, the defendant, and the judge simultaneously, and the default judgment is “guilty.” It can exonerate itself only by, at its own expense and peril, producing a written record of the evidence examined. This procedural hurdle is designed to simplify review by the United States’ actual legal system, regulators, and consumer advocates.
The institution's report of the results of its investigation shall include a written explanation of the institution's findings and shall note the consumer's right to request the documents that the institution relied on in making its determination. Upon request, the institution shall promptly provide copies of the documents.
Having done informal consumer advocacy for people with banking and debt issues for a few years, I cannot overstate the degree to which this prong of Reg E is a gift to consumer advocates. Many consumers are not impressively detail-oriented, and Reg E allows an advocate to conscript a financial institution’s Operations department to backfill the customer’s files about a transaction they do not have contemporaneous records of. In the case that the Operations department itself isn’t organized, great, at least from my perspective. Reg E says the bank just ate the loss. And indeed, several times over the years, the prototypical grandmother in Kansas received a letter from a bank vice president of consumer lending explaining that the bank was in receipt of her Reg E complaint, had credited her checking account, and considered the matter closed. It felt like a magic spell to me at the time.
Banks do not like losing money, citation hopefully unnecessary, and part of the business of banking is arranging for liability transfers. Insurance is many peoples’ paradigmatic way to understand liability transfers, but banks make minimal use of insurance in core banking services. (A bank which is robbed almost always self-insures, and the loss—averaging four figures and trending down—is so tiny that it isn’t worth specifically budgeting for.)
The liability transfer which most matters to Reg E is a contractual one, from issuing banks to card processors and from card processors to card-accepting businesses. These parties’ obligations to banks and cardholders are substantially broader than the banks’ obligations under Reg E, but the banks use a fraction of those contracts to defray a large portion of their Reg E liability.
For example, under the various brands’ card rules, an issuer must have the capability for a customer to say that a transaction which happened over plastic (or the electronic equivalent) simply didn’t meet their expectations. The issuer’s customer service representative will briefly collect facts from the customer, and then initiate an automatic process to request information from a representative of the card-accepting business. On receipt of that information, or non-receipt of it, a separate customer service representative makes a decision on the case. This mechanism is called a “chargeback” in the industry, and some banks are notorious for favoring the high-income quite-desirable customers who hold their plastic over the e.g. restaurant that the bank has no relationship with. “My eggs were undercooked” is a sufficient reason to ask for a chargeback and will result in the bank restoring your money a large percentage of the time.
In the case where the complaint is “My card was stolen and used without my knowledge”, essentially the same waterfall activates, perhaps with the internal note made that this dispute is Reg E sensitive. But mechanically it will be quite similar: bank tells processor “Customer asserts fraud”, processor tells business, business replies with a fax, bank staff reviews fax and adjudicates.
There are on the order of 5 million criminal cases in the formal U.S. legal system every year. There are more than 100 million complaints to banks, some of them alleging a simple disagreement (undercooked eggs) and very many alleging crime (fraud). It costs banks billions of dollars to adjudicate them.
The typical physical form of an adjudication is not a weeks-long trial with multiple highly-educated representatives debating in front of a more-senior finder of fact. It is a CSR clicking a button on their web app’s interface after 3 minutes of consideration, and then entire evidentiary record often fits in a tweet.
“Customer ordered from online store. Customer asserts they didn’t receive the item in six weeks. No response from store. Customer wins. Next.”, “Customer ordered from online store. Customer asserts they didn’t receive item. Store provided evidence of shipping via UPS. Customer does not have a history of fraudulent chargebacks. Customer wins. Next.”, “Customer’s bookkeeper asserts ignorance of software as a service provider charge. Business provided written statement from customer’s CEO stating chargeback filed in error by new bookkeeper. Customer wins. Next.” (I’m still annoyed by that last one, years later, but one has to understand why it is rational for the bank and, in a software company’s clearer-minded moments, rational for them to accept the risk of this given how lucrative software is.)
The funds flow in a chargeback mirrors the contractual liability waterfall: the issuing bank gets money back from a financial intermediary, who gets it back from a card processor (like Stripe, which I once worked for, and which doesn’t specifically endorse things I write in my own spaces), who will attempt to get it back from the card accepting business.
That word “attempt” is important. What if the business doesn’t have sufficient money to pay the aggrieved customer, or they can’t be located anymore when the system comes to collect? Reg E has a list of exceptions and those aren’t on it. The card processor then eats the loss.
The same frequently happens to cover the provisional credit mandated while the bank does its investigation, and the opposite happens in the case where the issuing bank decides that the card accepting business is in the right, and should be restored the money they charged a customer.
This high-frequency privately-funded alternative legal system has quietly ground out hundreds of millions of cases for the last half century. It is a foundation upon which commerce rests. It even exerts influence internationally, since the card brand rules essentially embed a variant of the Reg E rights for cardholders globally, and since nowhere in Reg E is there a carveout for transactions that a customer might make electronically with their U.S. financial institution while not physically located in the United States. If you are mugged and forced to withdraw money at an ATM in Caracas, Uncle Sam says your bank knows that some tiny percentage of cardholders will be mugged every year, and mandates they pay.
Zelle, operated by Early Warning Systems (owned by a consortium of large banks), is a substantially real-time electronic transfer method between U.S. bank accounts. Bank web and mobile apps have for decades supported peer to peer and customer to business transfers, via push ACH (and, less frequently, by wire), but ACH will, in standard practice, take a few days to be credited to the recipient and a few hours until it will become known to them as pending.
Zelle is substantially a blocking play, against Venmo, Cash App, and similar. Those apps captivated a large number of mostly-young users with the P2P payments, for use cases like e.g. splitting dinner, spotting a buddy $20, or collecting donations for a Christmas gift for the teacher from all the parents in a class. After attracting the users with those features, they kept them with product offerings which, in the limit, resemble bank accounts and which actually had bank accounts under the hood for at least some users.
And so the banks, fearing that real-time payment rails would not arrive in time (FedNow has been FedLater for a decade and RTP has relatively poor coverage), stood up Zelle, on the theory that this feature could be swiftly built into all the bank apps. Zelle launched in 2017.
Zelle processes enormous volumes. It crowed recently that it did $600 billion in volume in the first half of 2025. Zelle is much larger than the upstarts like Venmo (about $250 billion in annual volume) and Cash App (about $300 billion in customer inflows annually). This is not nearly in the same league as card payments (~$10 trillion annually) or ACH transfers (almost $100 trillion annually), but it is quite considerable.
All of it is essentially free to the transacting customers, unlike credit cards, which are extremely well-monetized. And there is the rub.
“Hiya, this is Susan calling from your bank. Your account has been targeted by fraudsters. I need you to initiate a Zelle payment to yourself to move it to a safe account while we conduct our investigation. Just open your mobile banking app, type the password, select Zelle from the menu, and send it to your own phone number. Thank you for your cooperation.”
Susan is lying. Her confederates have convinced at least one financial institution in the U.S. that the customer’s phone number is tied to a bank account which fraudsters control. That financial institution registered it with Zelle, so that when the victim sends money, the controlled account receives it substantially instantaneously. They will then attempt to immediately exfiltrate that money, sending it to another financial institution or a gift card or a crypto exchange, to make it difficult for investigators to find it faster than they can spend it. This process often repeats; professionals call this “layering.”
So, some days later, when the victim calls the bank and asks what happened to the money the bank was trying to secure from fraud, what does the bank tell them?
Zelle is quick to point out that only 0.02% of transactions over it have fraud reported, and they assert this compares favorably to competing payments methods. Splendid, then do the banks want to absorb on the order of $240 million a year in losses from fraudulent use of a technology they built into their own apps which is indisputably by any intellectually serious person an electronic funds access device?
Frequently in the last few years, the bank has said “Well, as Gen Z would say, that sounds like a bit of a skill issue.” And Reg E? “We never heard of it. Caveat emptor.”
To be slightly more sympathetic to the banks, they’re engaged in fine-grained decisioning on Zelle frauds, which have many mechanisms and flavor texts. They are more likely to reimburse as required in the case of account takeovers, where the criminal divines a customer’s password, pops an email address, or steals access to a phone number, and then uses it to empty a bank account. They are far less likely to reimburse where the criminal convinces the customer to operate their access device (mobile phone) in a way against their interests. Skill issue.
Why do banks aggressively look for reasons to deny claims? Elementary: there is no waterfall for Zelle. If there is a reimbursement for the user, it has to come from the bank’s balance sheet. (Zelle as originally shipped was incapable of reversing a transaction to claw back funds. That mechanism was something of an antipriority at design time, since funds subject to a clawback might be treated by receiving banks as non-settled, and the user experience banks wanted to deliver was “instantly spendable, like on Venmo.” Instantaneous funds availability exists in fundamental tension with security guarantees even if the finality gets relaxed, as Zelle’s was in 2023 under regulatory pressure.)
Banks like to pretend that the dominant fraud pattern is e.g. a “social media scam”, where an ad on Facebook or a Tiktok video leads someone to purchase sneakers with a Zelle payment from an unscrupulous individual, who doesn’t actually send the sneakers. This pattern matches more towards “well, that’s a disagreement about how your eggs were done, not a disagreement about how we operate payment rails.” Use a card and we’ll refund the eggs (via getting the restaurant to pay for them); don’t and we won’t.
So, in sum and in scaled practice at call centers, the bank wants to quickly get customers to admit their fingers were on their phone when defrauded. If so, no reimbursement.
This rationale is new and is against our standard practice, for decades. If you are defrauded via a skimming device attached to an ATM, the bank is absolutely liable, and will almost always come to the correct conclusion immediately. It would be absurdly cynical to say that you intended to transact with the skimming device and demonstrated your assent by physically dipping your card past it.
Bank recalcitrance caused the Consumer Financial Protection Bureau to sue a few large banks in late 2024. The CFPB alleged they had a pattern and practice of not paying out claims for fraud conducted over Zelle rails. The banks will tell you the same, using slightly different wording. Chase, for example, now buries in the fine print “Neither Chase nor Zelle® offers reimbursement for authorized payments you make using Zelle®, except for a limited reimbursement program that applies for certain imposter scams where you sent money with Zelle®. This reimbursement program is not required by law and may be modified or discontinued at any time.”
The defensible gloss of banks’ position on “purchase protection” is that the purchase protection that customers pay for in credit cards which makes them whole for eggs not cooked to their liking is not available for Zelle payments. Fine.
The indefensible extension is that banks aren’t liable for defrauded customers. That is a potential policy regime, chosen by the polity of many democratic nations. The United States is not one of those nations. Our citizens, through their elected representatives, made the considered choice that financial institutions would need to provide extraordinary levels of safety in electronic payments. In reliance upon that regime, the people of the United States transacted many trillions of dollars over payment rails, which was and is very lucrative for all considered.
The CFPB’s lawsuit was dropped in early 2025, as CFPB’s enforcement priorities were abruptly curtailed. (Readers interested in why might see Debanking and Debunking and Ctrl-F “wants some examples made.”) To the extent it still exists after being gutted, it is fighting for its life.
But knifing the CFPB doesn’t repeal Reg E. In theory, any bank regulator (and many other actors besides) can hold them to account for obligations under it. One of the benefits of Reg E is that the single national standard is easiest to reason about, but in the absence of it, one can easily imagine a patchwork of state-by-state consumer protection actions and/or coalitioning between state attorneys general. I will be unmoved if banks complain that this is all so complicated and they welcome regulation but it has to be a single national standard.
Having for the moment renegotiated their Reg E obligations by asserting they don’t exist, and mostly getting away with it, some banks might attempt to feel their oats a bit and assert that customers bear fraud risks more generally.
For example, in my hometown of Chicago, there has been a recent spate of tap-to-pay donation fraud. The fraudster gets a processing account, in their own name or that of a confederate/dupe, to collect donations for a local charitable cause. (This is not in itself improper; the financial industry understands that the parent in charge of a church bake sale will not necessarily be able to show paperwork to that effect before the cookies go stale.) Bad actors purporting to be informal charities accost Chicagoans on the street and ask for a donation via tap-to-pay, but the actual charged donation was absurdly larger than what the donor expected to donate; $4,000 versus $10, for example. The bad actor then exits the scene quickly.
(A donor who discovers the fraud in the moment is then confronted with the unfortunate reality that they are outnumbered by young men who want to rob them. This ends about as well as you’d expect. Chicago has an arrest rate far under 1% for this. A cynic might say that if you don’t kill the victim, it’s legal. I’m not quite that cynical.)
But Reg E doesn’t care about the safety of city streets, in Chicago or anywhere else. It assumes that payment instruments will continue to be used in an imperfect world. This case has a very clear designed outcome: customer calls bank, bank credits customer $4,000 because the customer was defrauded and therefore the “charity” lacked actual authority for the charge, bank pulls $4,000 from credit card processor, credit card processor attempts to pull $4,000 from the “charity”, card processor fails in doing so, card processor chalks it up to tuition to improve its fraud models in the future.
Except at least some banks, per the Chicago Tribune’s reporting, have adopted specious rationales to deny these claims. Some victims surrender physical control of their device, and banks argue that that means they authorized the transaction. Some banks asserted the manufactured-out-of-their-hindquarters rationale that Reg E only triggers when there is a physical receipt. (This inverts the Act’s responsibility graph, where banks were required to provide physical hardcopy receipts to avoid an accountability sink swallowing customer funds.)
Banks will often come to their senses after being contacted by the Chicago Tribune or someone with social power and gravitas who knows how to cite Reg E. But it is designed to work even for less sophisticated customers who don’t know the legislative history of the state machine. They just have to know “Call your bank if you have a problem.”
That should work and we are diminished if it doesn’t.
With a limited number of carveouts (e.g. wire transfers), Reg E is intentionally drafted to be future-proof against changes in how Americans transact. This is why, when banks argue that some new payments rail is exempt because it is “different,” the correct legal response is usually some variation of: doesn’t matter—that’s Reg E.
Our friends in crypto generally believe that Reg E is one star in the constellation of regulations that they’re not subject to. They created Schrödinger’s financial infrastructure, which is the future of finance in the boardroom and just some geeks playing with an open source project once grandma gets defrauded. There is an unresolved tension in saying “Traditional institutions like Visa are adopting stablecoins” and in the see-no-evil reimburse-no-losses attitude issuers and others in the industry take towards fraud which goes over their rails.
Reg E doesn’t have an exception in its text for electronic funds transfers which happen over slow databases.
A hypothetical future CFPB, given the long-standing premise that fraud is not an acceptable outcome of consumer payment systems, would swiftly come to the conclusion that if it walks like a checking account, quacks like a checking account, and is marketed as an alternative to checking accounts, then it is almost certainly within Reg E scope.
Casting one’s eyes across the fintech landscape, many players seem to have checking account envy. In the era of the “financial superapp” where everyone wants to bolt on high-frequency use cases like payments to e.g. AUM gathering machines like brokerage accounts, that is worth a quick chat with Legal before you start getting the letters from Kansan grandmas.
[0] The first “credit cards” were not the plastic-with-a-magstripe form factor which came to dominate but rather “charge plates.” They were physical tokens which pointed at a record at e.g. a department store’s internal accounts, usually by means of an embossed account number, to be read by the Mk 0 human eyeball and, later, physically copied to a paper record via ink. Many were metal and designed to be kept around a key ring. As Matt Levine and many others have mentioned, the crypto community has speedrun hundreds of years of financial history, and keeping your account identifier on etched metal enjoyed a short renaissance recently. Unlike the department stores’ bookkeepers, crypto enthusiasts lost many millions of dollars of customer funds by misplacing their metal (see page 20 particularly).
[1] Market research in the 1950s was hard. Short version of the Fresno drop: they lost money due to abuse by a small segment of users, but successfully proved that the middle class would happily use plastic to transact if they were offered it and it was generally accepted by businesses as opposed to being tied to a single store. They then scaled the 60,000 card pilot to millions within a year. Visa is the corporate descendant of that program; Mastercard that of what competitors did in response.
2025-12-20 04:45:06

Programming note: Merry Christmas! There will likely be another Bits about Money after the holiday but before New Year.
Bits about Money is supported by our readers. If your education budget or business can underwrite the coming year of public goods in financial-infrastructure education, commentary, and policy analysis, please consider supporting it. I’m told this is particularly helpful for policymakers and others who cannot easily expense a subscription, and who benefit from all issues remaining publicly available with no paywall.
The American Association of Retired People (AARP, an advocacy non-profit for older adults) has paid for ads on podcasts I listen to. The ad made a claim which felt raspberry-worthy (in service of an important public service announcement), which they repeat in writing: Asking to be paid by gift card is always a scam.
Of course it isn’t. Gift cards are a payments rail, and an enormous business independently of being a payments rail. Hundreds of firms will indeed ask you to pay them on gift cards! They also exist, and are marketed, explicitly to do the thing that the AARP implicitly asserts no business or government entity will ever do: provide a method for transacting for people who do not have a banked method of transacting. [0]
Gift card scams are also enormous. The FBI’s Internet Crime Complaint Center received $16.6 billion in reports in 2024 across several payment methods; this is just for those consumers who bothered reporting it, in spite of the extremely real received wisdom that reporting is unlikely to improve one’s direct situation.
The flavor texts of scams vary wildly, but in substance they’ll attempt to convince someone, often someone socially vulnerable, to part with sometimes very large sums of money by buying gift cards and conveying card information (card number and PIN number, both printed on the card) to the scammer. The scammer will then use the fraud supply chain, generally to swap the value on the card to another actor in return for value unconnected to the card. This can be delivered in many ways: cash, crypto, products and services in the scamming economy (such as purloined credit cards or even “lead lists” of vulnerable people to run more scams on), or laundered funds within regulated financial institutions which obscure the link between the crime and the funds (layering, in the parlance of AML professionals). A huge portion of running a gift card marketplace is trying to prevent yourself from being exploited or made into an instrumentality in exploiting others.
It surprises many people to learn that the United States aggressively defends customers from fraud over some payment methods, via a liability transfer to their financial institution, which transfers it to intermediaries, who largely transfer it to payment-accepting businesses. Many people think the U.S. can’t make large, effective, pro-consumer regulatory regimes. They are straightforwardly wrong… some of the time.
But the AARP, the FBI, and your friendly local payments nerd will all tell you that if you’re abused on your debit card you are quite likely to be made whole, and if you’re abused via purchasing gift cards, it is unlikely any deep pockets will cover for you. The difference in treatment is partially regulatory carveouts, partially organized political pressure, and partly a side effect of an accountability sink specific to the industrial organization of gift cards.
There exists an ecosystem of gift card program managers, who are essentially financial services businesses with a sideline in software. (I should probably mention that I previously worked for and am currently an advisor to Stripe, whose self conception would not be precisely that, but which a) supports many ways for people to pay money for things and b) does not necessarily endorse what I say in my personal spaces.)
Why does the program manager exist? Why not simply have the retailer keep some internal database of who the retailer owes money to, updating this when someone buys or loads a gift card and when they spend the balance at the store? Because this implies many capabilities that retailers do not necessarily have, such as e.g. software development teams.
There is also a large regulatory component to running a gift card program, despite gift cards’ relatively lax regulatory drag (we’ll return to that in a moment). Card programs are regulated at both the federal and state levels. One frequent requirement in several states is escheatment. (Essentially all states have a requirement for escheatment; many but not all exempt gift cards from it.)
As discussed previously in Bits about Money, a major component of the gift card business model is abandonment (“breakage”). Consumer advocates felt this was unfair to consumers, bordering on fraudulent really. They convinced states to take the money that retailers were keeping for themselves. (Many states didn’t take all that much convincing.)
In theory, and sometimes even in practice, a consumer can convince a state treasurer’s office of unclaimed property (e.g. Illinois’) that the $24.37 that Target remitted as part of its quarterly escheatment payment for an unused gift card 13 years ago was actually theirs. A consumer who succeeds at this, which is neither easy nor particularly inexpensive to do, will receive a $24.37 check in the mail. The state keeps the interest income; call it a fee for service. It also keeps the interest income of the tens of billions of dollars of accumulated unclaimed property, which it generally promises to dutifully custody awaiting a legitimate claim for as long as the United States shall exist.
And so if you are a regional or national retailer who wants to offer gift cards, you have a choice. You can dedicate a team of internal lawyers and operations specialists to understanding both what the laws of the several states require with respect to gift cards, which are a tiny portion of your total operations, not merely today but as a result of the next legislative session in Honolulu, because you absolutely must order the software written to calculate the payment to remit accurately several quarters in advance of the legal requirement becoming effective. Or you can make the much more common choice, and outsource this to a specialist.
That specialist, the gift card program manager, will sell you a Solution™ which integrates across all the surfaces you need: your point-of-sale systems, your website, your accounting software, the 1-800 number and website for customers to check balances, ongoing escheatment calculation and remittance, cash flow management, carefully titrated amounts of attention to other legal obligations like AML compliance, etc. Two representative examples: Blackhawk Network and InComm Payments. You’ve likely never heard of them, even if you have their product on your person right now. Their real customer has the title Director of Payments at e.g. a Fortune 500 company.
And here begins the accountability sink: by standard practice and contract, when an unsophisticated customer is abused by being asked to buy a BigCo gift card, BigCo will say, truthfully and unhelpfully, that BigCo does not issue BigCo gift cards. It sells them. It accepts them. But it does not issue them. Your princess is in another castle.
BigCo may very well have a large, well-staffed fraud department. But, not due to any sort of malfeasance whatsoever, that fraud department may consider BigCo gift cards entirely out of their own scope. They physically cannot access the database with the cards. Their security teams, sensitive that gift card numbers are dangerous to keep lying around, very likely made it impossible for anyone at BigCo to reconstruct what happened to a particular gift card between checkout and most recent use. “Your privacy is important to us!” they will say, and they are not cynically invoking it in this case.
As mentioned above, Regulation E is the primary driver for the private enforcement edifice that makes scarily smart professionals (and their attached balance sheets) swing into action on behalf of consumers. Reg E has a carveout for certain prepaid payments. Per most recent guidance, that includes prepaid gift cards, gift certificates, and similar.
And so, if you call your bank and say, “I was defrauded! Someone called me and pretended to be the IRS, and I read them my debit card number, and now I’ve lost money,” the state machine obligates the financial institution to have the customer service representative click a very prominent button on their interface. This will restore your funds very quickly and have some side effects you probably care about much less keenly. One of those is an “investigation,” which is not really an investigation in the commanding majority of cases.
And if you call the program manager and say, “I was defrauded! Someone called me and pretended to be the IRS, and I read them a gift card number, and now I’ve lost money,” there is… no state machine. There is no legal requirement to respond with alacrity, no statutorily imposed deadline, no button for a CS rep to push, and no investigation to launch. You will likely be told by a low-paid employee that this is unfortunate and that you should file a police report. The dominant reason for this is that suggesting a concrete action to you gets you off the phone faster, and the call center aggressively minimizes time to resolution of calls and recidivism, where you call back because your problem is not solved. Filing a police report will, in most cases, not restore your money—but if it causes you not to call the 1-800 number again, then from the card program manager’s perspective this issue has been closed successfully.
The people of the United States, through their elected representatives and the civil servants who labor on their behalf, intentionally exempt gift cards from the Reg E regime in the interest of facilitating commerce.
It is the ordinary and appropriate work of a democracy to include input from citizens in the rulemaking process. The Retail Industry Leaders Association participated, explaining to FinCEN that it would be quite burdensome for retailers to fall into KYC scope, etc etc. Many other lobbyists and industry associations made directionally similar comments.
The Financial Crimes Enforcement Network, for example, has an explicit carveout in its regulations: while FinCEN will aggressively police rogue bodegas, it has no interest in you if you sell closed-loop gift cards of less than $2,000 face value. This is explicitly to balance the state’s interest in law enforcement against, quote, preserving innovation and the many legitimate uses and societal benefits offered by prepaid access, endquote.
FinCEN’s rules clarify that higher-value activity—such as selling more than $10,000 in gift cards to a single individual in a day—brings sellers back into scope. Given the relatively lax enforcement environment for selling a $500 gift card, you very likely might not build out systems which will successfully track customer identities and determine that the same customer has purchased twenty-one $500 gift cards in three transactions. That likely doesn’t rate as a hugely important priority for Q3.
And so the fraud supply chain comes to learn which firms haven’t done that investment, and preferentially suggests those gift cards to their launderers, mules, brick movers, and scam victims.
And that’s why the AARP tells fibs about gift cards: we have, with largely positive intentions and for good reasons, exposed them to less regulation than most formal payment systems in the United States received. That decision has a cost. Grandma sometimes pays it.
[0] Indeed, there are entire companies which exist to turn gift cards into an alternate financial services platform, explicitly to give unbanked and underbanked customers a payments rail. Paysafe, for example, is a publicly traded company with thousands of employees, the constellation of regulatory supervision you’d expect, and a subsidiary Openbucks which is designed to give businesses the ability to embed Pay Us With A Cash Voucher in their websites/invoices/telephone collection workflows. This is exactly the behavior that “never happens from a legitimate business” except when it does by the tens of billions of dollars.
As Bits about Money has frequently observed, people who write professionally about money—including professional advocates for financially vulnerable populations—often misunderstand alternative financial services, largely because those services are designed to serve a social class that professionals themselves do not belong to, rarely interact with directly, and do not habitually ask how they pay rent, utilities, or phone bills.
2025-12-06 05:16:46

Programming note: Bits about Money is supported by our readers. I generally forecast about one issue a month, and haven't kept that pace that this year. As a result, I'm working on about 3-4 for December.
Much financial innovation is in the ultimate service of the real economy. Then, we have our friends in crypto, who occasionally do intellectually interesting things which do not have a locus in the real economy. One of those things is perpetual futures (hereafter, perps), which I find fascinating and worthy of study, the same way that a virologist just loves geeking out about furin cleavage sites.
You may have read a lot about stablecoins recently. I may write about them (again; see past BAM issue) in the future, as there has in recent years been some uptake of them for payments. But it is useful to understand that a plurality of stablecoins collateralize perps. Some observers are occasionally strategic in whether they acknowledge this, but for payments use cases, it does not require a lot of stock to facilitate massive flows. And so of the $300 billion or so in stablecoins presently outstanding, about a quarter sit on exchanges. The majority of that is collateralizing perp positions.
Perps are the dominant way crypto trades, in terms of volume. (It bounces around but is typically 6-8 times larger than spot.) This is similar to most traditional markets: where derivatives are available, derivative volume swamps spot volume. The degree to which depends on the market, Schelling points, user culture, and similar. For example, in India, most retail investing in equity is actually through derivatives; this is not true of the U.S. In the U.S., most retail equity exposure is through the spot market, directly holding stocks or indirectly through ETFs or mutual funds. Most trading volume of the stock indexes, however, is via derivatives.
The large crypto exchanges are primarily casinos, who use the crypto markets as a source of numbers, in the same way a traditional casino might use a roulette wheel or set of dice. The function of a casino is for a patron to enter it with money and, statistically speaking, exit it with less. Physical casinos are often huge capital investments with large ongoing costs, including the return on that speculative capital. If they could choose to be less capital intensive, they would do so, but they are partially constrained by market forces and partially by regulation.
A crypto exchange is also capital intensive, not because the website or API took much investment (relatively low, by the standards of financial software) and not because they have a physical plant, but because trust is expensive. Bettors, and the more sophisticated market makers, who are the primary source of action for bettors, need to trust that the casino will actually be able to pay out winnings. That means the casino needs to keep assets (generally, mostly crypto, but including a smattering of cash for those casinos which are anomalously well-regarded by the financial industry) on hand exceeding customer account balances.
Those assets are… sitting there, doing nothing productive. And there is an implicit cost of capital associated with them, whether nominal (and borne by a gambler) or material (and borne by a sophisticated market making firm, crypto exchange, or the crypto exchange’s affiliate which trades against customers [0]).
Perpetual futures exist to provide the risk gamblers seek while decreasing the total capital requirement (shared by the exchange and market makers) to profitably run the enterprise.
In the commodities futures markets, you can contract to either buy or sell some standardized, valuable thing at a defined time in the future. The overwhelming majority of contracts do not result in taking delivery; they’re cancelled by an offsetting contract before that specified date.
Given that speculation and hedging are such core use cases for futures, the financial industry introduced a refinement: cash-settled futures. Now there is a reference price for the valuable thing, with a great deal of intellectual effort put into making that reference price robust and fair (not always successfully). Instead of someone notionally taking physical delivery of pork bellies or barrels of oil, people who are net short the future pay people who are net long the future on delivery day. (The mechanisms of this clearing are fascinating but outside today’s scope.)
Back in the early nineties economist Robert Shiller proposed a refinement to cash settled futures: if you don’t actually want pork bellies or oil barrels for consumption in April, and we accept that almost no futures participants actually do, why bother closing out the contracts in April? Why fragment the liquidity for contracts between April, May, June, etc? Just keep the market going perpetually.
This achieved its first widespread popular use in crypto (Bitmex is generally credited as being the popularizer), and hereafter we’ll describe the standard crypto implementation. There are, of course, variations available.
Instead of all of a particular futures vintage settling on the same day, perps settle multiple times a day for a particular market on a particular exchange. The mechanism for this is the funding rate. At a high level: winners get paid by losers every e.g. 4 hours and then the game continues, unless you’ve been blown out due to becoming overleveraged or for other reasons (discussed in a moment).
Consider a toy example: a retail user buys 0.1 Bitcoin via a perp. The price on their screen, which they understand to be for Bitcoin, might be $86,000 each, and so they might pay $8,600 cash. Should the price rise to $90,000 before the next settlement, they will get +/- $400 of winnings credited to their account, and their account will continue to reflect exposure to 0.1 units of Bitcoin via the perp. They might choose to sell their future at this point (or any other). They’ll have paid one commission (and a spread) to buy, one (of each) to sell, and perhaps they’ll leave the casino with their winnings, or perhaps they’ll play another game.
Where did the money come from? Someone else was symmetrically short exposure to Bitcoin via a perp. It is, with some very important caveats incoming, a closed system: since no good or service is being produced except the speculation, winning money means someone else lost.
One fun wrinkle for funding rates: some exchanges cap the amount the rate can be for a single settlement period. This is similar in intent to traditional markets’ usage of circuit breakers: designed to automatically blunt out-of-control feedback loops. It is dissimilar in that it cannot actually break circuits: changes to funding rate can delay realization of losses but can’t prevent them, since they don’t prevent the realization of symmetrical gains.
Perp funding rates also embed an interest rate component. This might get quoted as 3 bps a day, or 1 bps every eight hours, or similar. However, because of the impact of leverage, gamblers are paying more than you might expect: at 10X leverage that’s 30 bps a day. Consumer finance legislation standardizes borrowing costs as APR rather than basis points per day so that an unscrupulous lender can’t bury a 200% APR in the fine print.
Prices for perps do not, as a fact of nature, exactly match the underlying. That is a feature for some users.
In general, when the market is exuberant, the perp will trade above spot (the underlying market). To close the gap, a sophisticated market participant should do the basis trade: make offsetting trades in perps and spot (short the perp and buy spot, here, in equal size). Because the funding rate is set against a reference price for the underlying, longs will be paying shorts more (as a percentage of the perp’s current market price). For some of them, that’s fine: the price of gambling went up, oh well. For others, that’s a market incentive to close out the long position, which involves selling it, which will decrease the price at the margin (in the direction of spot).
The market maker can wait for price convergence; if it happens, they can close the trade at a profit, while having been paid to maintain the trade. If the perp continues to trade rich, they can just continue getting the increased funding cost. To the extent this is higher than their own cost of capital, this can be extremely lucrative.
Flip the polarities of these to understand the other direction.
The basis trade, classically executed, is delta neutral: one isn’t exposed to the underlying itself. You don’t need any belief in Bitcoin’s future adoption story, fundamentals, market sentiment, halvings, none of that. You’re getting paid to provide the gambling environment, including a really important feature: the perp price needs to stay reasonably close to the spot price, close enough to continue attracting people who want to gamble. You are also renting access to your capital for leverage.
You are also underwriting the exchange: if they blow up, your collateral becoming a claim against the bankruptcy estate is the happy scenario. (As one motivating example: Galois Capital, a crypto hedge fund doing basis trades, had ~40% of its assets on FTX when it went down. They then wound down the fund, selling the bankruptcy claim for 16 cents on the dollar.)
Recall that the market can’t function without a system of trust saying that someone is good for it if a bettor wins. Here, the market maker is good for it, via the collateral it kept on the exchange.
Many market makers function across many different crypto exchanges. This is one reason they’re so interested in capital efficiency: fully collateralizing all potential positions they could take across the universe of venues they trade on would be prohibitively capital intensive, and if they do not pre-deploy capital, they miss profitable trading opportunities. [1]
Gamblers like risk; it amps up the fun. Since one has many casinos to choose from in crypto, the ones which only “regular” exposure to Bitcoin (via spot or perps) would be offering a less-fun product for many users than the ones which offer leverage. How much leverage? More leverage is always the answer to that question, until predictable consequences start happening.
In a standard U.S. brokerage account, Regulation T has, for almost 100 years now, set maximum leverage limits (by setting minimums for margins). These are 2X at position opening time and 4X “maintenance” (before one closes out the position). Your brokerage would be obligated to forcibly close your position if volatility causes you to exceed those limits.
As a simplified example, if you have $50k of cash, you’d be allowed to buy $100k of stock. You now have $50k of equity and a $50k loan: 2x leverage. Should the value of that stock decline to about $67k, you still owe the $50k loan, and so only have $17k remaining equity. You’re now on the precipice of being 4X leveraged, and should expect a margin call very soon, if your broker hasn’t “blown you out of the trade” already.
What part of that is relevant to crypto? For the moment, just focus on that number: 4X.
Perps are offered at 1X (non-levered exposure). But they’re routinely offered at 20X, 50X, and 100X. SBF, during his press tour / regulatory blitz about being a responsible financial magnate fleecing the customers in an orderly fashion, voluntarily self-limited FTX to 20X.
One reason perps are structurally better for exchanges and market makers is that they simplify the business of blowing out leveraged traders. The exact mechanics depend on the exchange, the amount, etc, but generally speaking you can either force the customer to enter a closing trade or you can assign their position to someone willing to bear the risk in return for a discount.
Blowing out losing traders is lucrative for exchanges except when it catastrophically isn’t. It is a priced service in many places. The price is quoted to be low (“a nominal fee of 0.5%” is one way Binance describes it) but, since it is calculated from the amount at risk, it can be a large portion of the money lost. If the account’s negative balance is less than the liquidation fee, wonderful, thanks for playing and the exchange / “the insurance fund” keeps the rest, as a tip.
In the case where the amount an account is negative by is more than the fee, that “insurance fund” can choose to pay the winners on behalf of the liquidated user, at management’s discretion. Management will usually decide to do this, because a casino with a reputation for not paying winners will not long remain a casino.
But tail risk is a real thing. The capital efficiency has a price: there physically does not exist enough money in the system to pay all winners given sufficiently dramatic price moves. Forced liquidations happen. Sophisticated participants withdraw liquidity (for reasons we’ll soon discuss) or the exchange becomes overwhelmed technically / operationally. The forced liquidations eat through the diminished / unreplenished liquidity in the book, and the magnitude of the move increases.
Then crypto gets reminded about automatic deleveraging (ADL), a detail to perp contracts that few participants understand.
(Pray we do not alter them further.)
Risk in perps has to be symmetric: if (accounting for leverage) there are 100,000 units of Somecoin exposure long, then there are 100,000 units of Somecoin exposure short. This does not imply that the shorts or longs are sufficiently capitalized to actually pay for all the exposure in all instances.
In cases where management deems paying winners from the insurance fund would be too costly and/or impossible, they automatically deleverage some winners. In theory, there is a published process for doing this, because it would be confidence-costing to ADL non-affiliated accounts but pay out affiliated accounts, one’s friends or particularly important counterparties, etc. In theory.
In theory, one likely ADLs accounts which were quite levered before ones which were less levered, and one ADLs accounts which had high profits before ones with lower profits. In theory. [2]
So perhaps you understood, prior to a 20% move, that you were 4X leveraged. You just earned 80%, right? Ah, except you were only 2X leveraged, so you earned 40%. Why were you retroactively only 2X? That’s what automatic deleveraging means. Why couldn’t you get the other 40% you feel entitled to? Because the collective group of losers doesn’t have enough to pay you your winnings and the insurance fund was insufficient or deemed insufficient by management.
ADL is particularly painful for sophisticated market participants doing e.g. a basis trade, because they thought e.g. they were 100 units short via perps and 100 units long somewhere else via spot. If it turns out they were actually 50 units short via perps, but 100 units long, their net exposure is +50 units, and they have very possibly just gotten absolutely shellacked.
In theory, this can happen to the upside or the downside. In practice in crypto, this seems to usually happen after sharp decreases in prices, not sharp increases. For example, October 2025 saw widespread ADLing as (more than) $19 billion of liquidations happened, across a variety of assets. Alameda’s CEO Caroline Ellison testified that they lost over $100 million during the collapse of Terra’s stablecoin in 2022, but since FTX’s insurance fund was made up; when leveraged traders lost money, their positions were frequently taken up by Alameda. That was quite lucrative much of the time, but catastrophically expensive during e.g. the Terra blowup. Alameda was a good loser and paid the winners, though: with other customers’ assets that they “borrowed.”
In the traditional markets, if one’s brokerage deems one’s assets are unlikely to be able to cover the margin loan from the brokerage one has used, one’s brokerage will issue a margin call. Historically that gave one a relatively short period (typically, a few days) to post additional collateral, either by moving in cash, by transferring assets from another brokerage, or by experiencing appreciation in the value of one’s assets. Brokerages have the option, and in some cases the requirement, to manage risk after or during a margin call by forcing trades on behalf of the customer to close positions.
It sometimes surprises crypto natives that, in the case where one’s brokerage account goes negative and all assets are sold, with a negative remaining balance, the traditional markets largely still expect you to pay that balance. This contrasts with crypto, where the market expectation for many years was that the customer was Daffy Duck with a gmail address and a pseudonymous set of numbered accounts recorded on a blockchain, and dunning them was a waste of time. Crypto exchanges have mostly, in the intervening years, either stepped up their game regarding KYC or pretended to do so, but the market expectation is still that a defaulting user will basically never successfully recover. (Note that the legal obligation to pay is not coextensive with users actually paying. The retail speculators with $25,000 of capital that the pattern day trade rules are worried about will often not have $5,000 to cover a deficiency. On the other end of the scale, when a hedge fund blows up, the fund entity is wiped out, but its limited partners—pension funds, endowments, family offices—are not on the hook to the prime broker, and nobody expects the general partner to start selling their house to make up the difference.)
So who bears the loss when the customer doesn’t, can’t, or won’t? The waterfall depends on market, product type, and geography, but as a sketch: brokerages bear the loss first, out of their own capital. They’re generally required to keep a reserve for this purpose.
A brokerage will, in the ordinary course of business, have obligations to other parties which would be endangered if they were catastrophically mismanaged and could not successfully manage risk during a downturn. (It’s been known to happen, and even can be associated with assets rather than liabilities.) In this case, most of those counterparties are partially insulated by structures designed to insure the peer group. These include e.g. clearing pools, guaranty funds capitalized by the member firms of a clearinghouse, the clearinghouse’s own capital, and perhaps mutualized insurance pools. That is the rough ordering of the waterfall, which varies depending geography/product/market.
One can imagine a true catastrophe which burns through each of those layers of protection, and in that case, the clearinghouse might be forced to assess members or allocate losses across survivors. That would be a very, very bad day, but contracts exist to be followed on very bad days.
One commonality with crypto, though: this system is also not fully capitalized against all possible events at all times. Unlike crypto, which for contingent reasons pays some lip service to being averse to credit even as it embraces leveraged trading, the traditional industry relies extensively on underwriting risk of various participants.
Many crypto advocates believe that they have something which the traditional finance industry desperately needs. Perps are crypto’s most popular and lucrative product, but they probably won’t be adopted materially in traditional markets.
Existing derivatives products already work reasonably well at solving the cost of capital issue. Liquidations are not the business model of traditional brokerages. And learning, on a day when markets are 20% down, that you might be hedged or you might be bankrupt, is not a prospect which fills traditional finance professionals with the warm fuzzies.
And now you understand the crypto markets a bit better.
[0] Brokers trading with their own customers can happen in the ordinary course of business, but has been progressively discouraged in traditional finance, as it enables frontrunning.
Frontrunning, while it is understood in the popular parlance to mean “trading before someone else can trade” and often brought up in discussions of high frequency trading using very fast computers, does not historically mean that. It historically describes a single abusive practice: a broker could basically use the slowness of traditional financial IT systems to give conditional post-facto treatment to customer orders, taking the other side of them (if profitable) or not (if not). Frontrunning basically disappeared because customers now get order confirms almost instantly by computer not at end of day via a phone call. The confirm has the price the trade executed at on it.
In classic frontrunning, you sent the customer’s order to the market (at some price X), waited a bit, and then observed a later price Y. If Y was worse for the customer than X, well, them’s the breaks on Wall Street. If Y was better, you congratulated the customer on their investing acumen, and informed them that they had successfully transacted at Z, a price of your choosing between X and Y. You then fraudulently inserted a recorded transaction between the customer and yourself earlier in the day, at price Z, and assigned the transaction which happened at X to your own account, not to the customer’s account.
Frontrunning was a lucrative scam while it lasted, because (effectively) the customer takes 100% of the risk of the trade but the broker gets any percentage they want of the first day’s profits. This is potentially so lucrative that smart money (and some investors in his funds!) thought Madoff was doing it, thus generating the better-than-market stable returns for over a decade through malfeasance. Of frontrunning Madoff was entirely innocent.
Some more principled crypto participants have attempted to discourage exchanges from trading with their own customers. They have mostly been unsuccessful: Merit Peak Limited is Binance’s captive entity which does this. It also is occasionally described by U.S. federal agencies as running a sideline in money laundering, Alameda Research was FTX’s affiliated trading fund. Their management was criminally convicted of money laundering. etc, etc.
One of the reasons this behavior is so adaptive is because the billions of dollars sloshing around can be described to banks as “proprietary trading” and “running an OTC desk”, and an inattentive bank (like, say, Silvergate, as recounted here) might miss the customer fund flows they would have been formally unwilling to facilitate. This is a useful feature for sophisticated crypto participants, and so some of them do not draw attention to the elephant in the room, even though it is averse to their interests.
[1] Not all crypto trades are pre-funded. Crypto OTC transactions sometimes settle on T+1, with the OTC desk essentially extending credit in the fashion that a prime broker would in traditional markets. But most transactions on exchanges have to be paid immediately in cash already at the venue. This is very different from traditional equity market structure, where venues don’t typically receive funds flow at all, and settling/clearing happens after the fact, generally by a day or two.
[2] I note, for the benefit of readers of footnote 0, that there is often a substantial gap between the time when market dislocation happens and when a trader is informed they were ADLed. The implications of this are left as an exercise to the reader.
2025-10-11 01:24:13
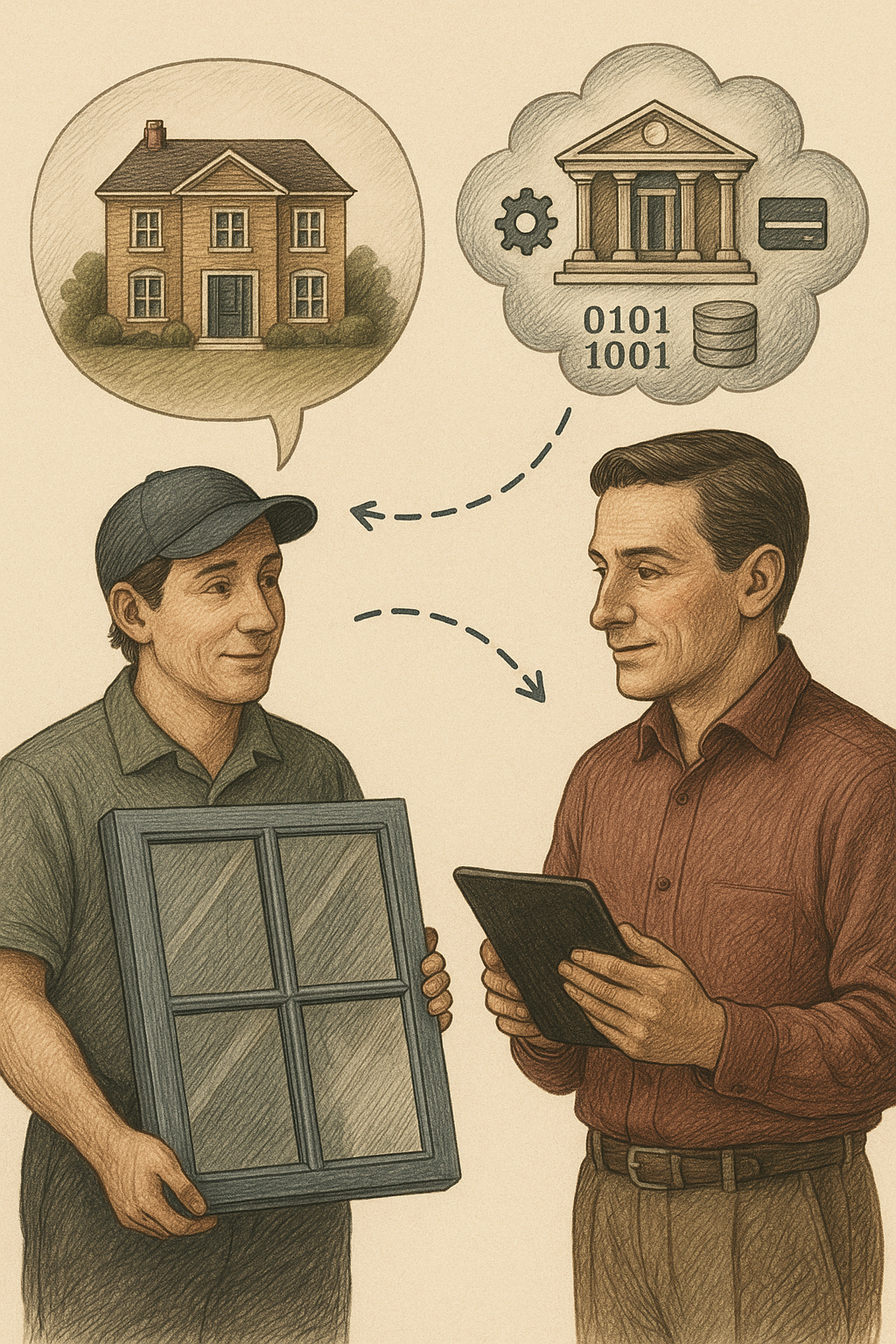
The ultimate goal of financial plumbing is to enable commerce in the real economy. Consider the humble window: it is a fairly expensive, surprisingly high-tech manufactured good, installed by the dozen in homes by artisans. A window represents a supply chain, and one part of that supply chain is a sales process, convincing a homeowner of the desirability of updating their windows. The sales representative running that process would urgently prefer to leave their single visit to the home with not just tentative measurements but with a durable commitment to buying the window and financing firmly in place for it.
Why finance the purchase? Windows cost $1,000 to $3,000 each and updating all or a large fraction of them quickly becomes a mid-five figures project; relatively few homeowners will pay upfront with cash. Moreover, the sales process would strongly prefer the purchase be financeable, because that will sell more windows than a counterfactual world where windows were only available for cash.
One could imagine a world in which window manufacturers or installers provided financing off of their own balance sheets. This would be a rough world for them: they have upfront capital outlay (the window) and would recoup only after extended periods, bearing credit risk all the while. No, they would prefer to sell windows for money. It’s frequently delivered in milestone payments, perhaps half prior to manufacturing the windows and half upon successful installation.
You could imagine the buyer could bring their own financing, perhaps by going to their usual bank and asking for a home improvement loan. That product very much exists, but it might be surprisingly less attractive to all parties: it will be costly, low margin for the bank, and have poor operational dynamics for the window company. And so you could imagine the window company asking the financial industry to come up with an alternative.
That alternative exists, and can underwrite and paperwork a four-party commercial loan in fifteen minutes, before the salesman has even left their home visit that sold the window. We’ll return to it in a moment.
Again, very many banks do actually make home improvement loans available. But they’re not wonderful loans for the banks.
We’ll begin with the somewhat awkward dollar amount: a home improvement loan is enough money to hurt if it goes bad, but not enough money to justify a high-volume well-oiled machine to underwrite, not like e.g. mortgages. And indeed that is what many banks will immediately try to sell you if you ask for a loan for the purpose of home improvement: can we instead counterpropose a home equity line of credit (HELOC)? You can then borrow against your existing home equity, withdrawing cash, and we have no objection to you swapping cash for a window, a decision we need hear no more about. We have a supply chain for mortgages, including HELOCs, and this supply chain will decrease our capital requirements while smoothing every part of underwriting.
Why does the bank want to take the window out of the window purchase? Because a home improvement loan otherwise requires multiple operationally intensive document reviews and conversations where bankers talk to construction company office managers. Those conversations are frequently unhappy ones.
Consider the case where a construction project flies off the rails, which has been known to happen. The window company says it has installed the windows, and potentially they have a certificate proving that they were indeed installed, allegedly signed by the homeowner or their spouse on the date of installation. The homeowner, however, is unhappy with the windows: they are drafty; the color isn’t the same as the brochure; and goodness was this what they agreed to pay e.g. $25,000 for?! They don’t want to pay it anymore.
The bank must be the adult in this scenario, to release that second milestone payment. They very possibly could be drawn into litigation over their decision, because a few tens of thousands of dollars is just enough to justify calling a lawyer. Then the bank will have to have their own lawyers defend their own contracts in an expensive proposition over what is, to it, a small-dollar loan.
It’s not nearly this hard to generate $25,000 of balances with a credit card issuing business. You mail out the cards and people buy airplane tickets. And then the airline pays you 200 basis points off the top even before you get to originate the high-interest loan! Great business to be in and you never have to talk about a stewardess spilling someone’s drink or it raining in Hawaii that week.
Meanwhile, the window installer has their own complaints about this loan, even before it is originated. Between the day the salesman shakes hands with the customer and the bank commits to the installation, they have very little they can do to influence success. The homeowner might develop buyer’s remorse and, while they might have signed a contract, it’s just rough to compel payment for windows which don’t exist yet. Your staff will not enjoy the process, your reviews will suffer, and it’s not guaranteed that your contract will hold up: in some states, your customer might even have legal right to sever during a cooling-off period. You would prefer to accelerate delivery to avoid them cooling on the idea of windows.
But the bank is slow and has a bespoke underwriting process which requires information from you but which you cannot control, because the window installer is not the bank’s customer. They can’t call the bank up and yell at the underwriters to move faster, and they can’t debate the bank over a credit decision, where a perfectly good sale gets nixed six weeks later because the bank just isn’t feeling it. Very few of those sales will result in the buyer arranging successful alternative financing, partly for very human reasons and partly for a mechanical one: the fact of the hard pull on the credit report for the original loan origination plus non-issuance of a loan from one’s home financial institution signals to the rest of the world “Oh goodness there are probably better ex-ante risks in the economy than this one!”
No, what the window installer wants is a lending product which can be issued at scale, very predictably, in as short a timeframe as possible, by financial institutions responsive to it who ask very few followup questions, always fund milestone payments promptly, and actually want this business.
That product exists.
Consumer credit issuance is, unless it comes directly from a manufacturer, a privilege reserved by law for regulated financial institutions. But, as we’ve established, regulated financial institutions don’t lust for this business on their own balance sheets at scale. (Recharacterizing the home improvement loan as a draw on a HELOC allows the bank to quickly get it off their balance sheet, because the HELOCs will generally be securitized. You could theoretically securitize a large pool of installment loans if you had a business process to generate them, but unless a bank specializes, they are unlikely to have core depositors simply ask for enough of these every year to justify building out the framework required to do this.)
Why is it reserved by law for financial institutions? As Bits about Money mentions often, financial institutions are a policy arm, and one thing the state requires is that Compliance make sure the financial institution is not abusing customers. The state believes that a e.g. window installer might use high-pressure sales tactics or say untrue things to a homeowner about how e.g. an interest-free financing period works, and then perhaps forget about those things when the customer complains. It believes, rationally, that financial institutions will keep extensive records of what they communicate about loans, that those records will be truthful by default, and that the financial institution will not endanger its permission to do business over a single product. Also, and this is a blunt but true observation, the state trusts white collar employees and executives at banks more than it trusts blue collar window installers.
So we need a bank involved, but that bank does not necessarily need to lend (from its own balance sheet). The bank could immediately sell a large portion of the loan, retaining perhaps 1% for form’s sake, to a private provider of capital.
But, again, it is unlikely that a bank will want to call around to hedge funds and see if there are any takers. Someone needs to have capital providers have a standing offer to snap at this product quickly.
That standing offer is variously called a forward funds flow agreement or warehouse financing. I’ve previously discussed the mechanics for Buy Now Pay Later (BNPL), and they’re the same here. Someone, typically a facilitator and not the bank itself, has brought the capital partners to the table, negotiated terms, and has prepared them to receive what they want: millions of dollars of loans, at attractive prices, with known-in-advance credit characteristics… originated by a massively scalable process, conducted partly by commission-earning sales reps bearing iPads into houses needing windows and partly by web applications and operational teams.
This machinery wasn’t originally perfected for windows. It was originally aimed mostly at solar installations, which were heavily tax-advantaged at the time. Capturing the tax credit required a sale and upfront capital outlay, and the pitch was essentially “Sign these loan docs for free money for all of us and, also, you’ll get some solar panels.” But the credits eventually expired, the addressable market for solar got more tapped, and the software and companies yearned for more originations. So, sign these documents, get windows at attractive prices.
The loan application begins with the customer verbally informing the salesman of their phone number or email address. They get given a link which swiftly brings them to a competently-designed web application. That application asks a few simple questions that are required for underwriting. The two most important ones that are not on a credit card application are “Is this your house?” and “Do you live in this house?” This is because the capital partners are much, much more confident that people will not welch on debts tied to their primary residence than that every real estate investor will be above water if 2008 happens again.
Questions about your finances are extremely pro-forma. You’ll be asked to self-state your income, but no attempt will be made to verify it. A credit report will be pulled, which satisfies the twin purposes of a) derisking the applicant pool and b) verifying, via checking for the presence of a mortgage, that you do actually own the house.
I ended up in a fraud queue at this point in the process. Story of my life. The facilitating company does not expose to the sales rep why you are in the fraud queue, but the clock is ticking, and the rep will (hypothetically) strongly prefer continuing to drink tea and chitchat rather than leaving and letting one resolve that issue asynchronously. It was resolved by a combination of automated submission of a passport photo (again, shockingly competent software by the historical standards of loan origination) and an analyst manually clicking a button in a web application.
If I were to speculate what that analyst was doing, it would be reviewing the facts: credit report says high credit score, credit report shows a mortgage, credit report does not match this address, but government-provided ID does match the asserted identity. And thus the wager: is he in his own house, or has he decided to pull a hilarious prank on a window installer and buy someone else windows with a hedge fund’s money? The analyst swiftly concluded I was probably in my own house. (Why did I end up in the fraud queue? I have a lot of weirdness, such as not being listed on the deed due to holding title through a land trust, for privacy reasons. Unfortunately, perhaps that sometimes makes it difficult for cron jobs to conclude I own the house.)
Once you’re approved for the loan, you are automatically sent loan documents for signature. This will not be compelled at the meeting, but the installer sure would appreciate you signing before they leave. Compliance has extensively briefed them on where the line is. Compliance has, in fact, extensively briefed them on many lines, and because Compliance cares more about the law than it does about paying programmers to code a login form, I was able to read their entire Compliance training series and presentations to installers.
Don’t lie. Don’t translate any loan docs from English or provide any gloss of the terms. Don’t say any of the forbidden phrases like “guaranteed approval”, “same-as-cash financing”, “interest-free financing”, etc. And definitely definitely do not touch their phone or computer during the application process.
The financial industry learned some things during the global financial crisis about aggressive salesmanship by its agents. Almost every bullet point in that 40 page PowerPoint has a stack of criminal convictions, billions of dollars of losses, or both to justify it.
The salesman will first quote a scary number designed to anchor you, then present the discount available if you commit within a month. They will then say there is a sweetener if and only if you sign before they leave. Compliance is very clear that if you say that in the context of acting as an agent for a financial institution it had better not be a lie, but percentages are percentages and window companies like making deals for windows, and I would not bet against the proposition that they would offer other inducements on other days for other reasons, perhaps summing to similar numbers.
They then present financing terms. I was pleasantly surprised that this was not presented in the typical obfuscating car dealer financing four square method. The real price stays onscreen on the iPad at all times and you are presented with columns for choices: pay cash (they mean immediately deliverable value, not actually specie), 12-month deferred interest financing, 15-year fixed rate financing, and pay in milestones (e.g. 50% deposit, 50% due on installation) on a credit card.
Compliance will inform representatives that you are absolutely not supposed to use the words “same as cash” and “interest-free” to describe 12 month deferred interest financing. This salaryman is unfortunately forgetful sometimes and so I cannot quite recall what the friendly local salesman actually said while pointing to the iPad. The offer is “If you fully pay for your windows within the next 12 months, you just pay the sticker price. If it takes you longer than that, you will pay us interest, starting from the date of installation, at a rate which is materially higher than the rate we quote in the next column.”
You might think, given that sketch, that the system is trying to trick naive homeowners and surprise them on day 366 with a nasty bill. I’m slightly more sympathetic. This offer is designed to be attractive to people who can bring their own financing without making the window installation dependent on that financing. If, for example, a customer does not currently have a HELOC, but is pretty sure they can get a HELOC, the window installer is saying “Great, convince any bank to give you a HELOC, then do a draw any time in the next year and repay us, and we’ll foot the interest until then. But to be clear this window is going in irrespective of your future discussions with banks. Our capital partners do not want you to attempt to skate if your financing falls through, if you get divorced, if your tax refund is smaller than expected, etc, and you will be penalized if you attempt to turn this into a backdoor installment loan.”
But the next column is where the real action is. I was quoted 6.99% APR for equal amortizing payments over 15 years. They, naturally, express this as a monthly number, but the contract floridly and in bold print (as required by regulations) discloses e.g. total interest cost over the life of the loan, the fact there is no pre-payment penalty, etc. This is as honest as consumer lending can possibly be.
You e-sign the loan documents and then the salesman thanks you for your time and arranges for another professional to come back and redundantly measure the windows. He measured for the quote, and the quote is good, but they’ll measure again because a quarter inch matters a lot more for the physical universe than it does for the spreadsheet. Then the order goes to the factory and, a few weeks later, they install the windows. You sign an acknowledgement, and then the automated software springs back into action, starting the clock on your interest and collecting payments.
Here I am going to speculate in reliance upon publicly available data sources rather than use information which I know as a result of private commercial negotiations. Window salesmen are not the only professionals who have been to Compliance training.
In the 15-minute window between the loan being applied for and signed, software has conducted a four-way commercial negotiation between the window installer, the facilitating entity, the bank, and the capital provider. The loan contract is between the customer and the bank (again, it has to be, regs) but the capital provider is a specialist institution.
There are a few banks which specialize in doing business like this. One of them is Cross River Bank, which keeps a keen eye on trends in consumer lending.
A bank which originates a loan might charge the facilitating entity an upfront fee-for-services, collect a servicing fee from the capital providers sliced out of the APR quoted to the customer, and of course retains actual economic interest in the loan… well, OK, a few hundred dollars of the loan, so that it can tell its regulators “No, really, we are lending money! It would be calumny to describe this situation as renting out a banking license!” Indicatively, that fee for services might look something like 1% of total loan volume, and the servicing fee might be 1% of the outstanding balance annually. (Mortgage servicing fees are about 0.25% but houses cost more than windows do and so you get an economy of scale. The servicing is essentially the same amount of work: you need a 1-800 number, lawyers on standby, the capability to receive checks, etc.)
So who is the capital provider and what are they getting? It will generally be a specialist fund, like say Sunlight Financial, whose name alludes to the solar business they got started in. You might naively assume “OK, 6.99% to the consumer, 1% servicing fee to the bank, so they get 5.99% APR on the loan, right?” I doubt that is the full calculation.
One reason is that loan sounds awfully cheap: the 10 year Treasury rate is currently a hair over 4%, so why would you give a consumer 15 years fixed rate financing for 6%? Even with excellent credit quality, 2% spread doesn’t sound like enough money to make a business out of this.
But: what if, like BNPLs, you could charge someone else a bit of money? Who benefits the most from this transaction? The window installer. So charge them for it. They’re clearly willing to pay something like 2.4% of the entire transaction size already, because they will happily let you buy windows with a credit card. So that’s the floor. A BNPL provider can charge Sephora something like 6% to sell lip gloss. That might be the ceiling. So can you get them to kick in… 5%? Probably.
That moves the APR as perceived by the lender to about 7.9%. (Ask Python or Excel if you don’t believe me.) It’s a bit better than this, too, because of what will happen to the fund if interest rates fall. The value of outstanding bonds increases if rates fall, but this consumer loan might get rolled into e.g. a newly cheap HELOC if rates fall. (The free no-penalty prepayment option is a fundamental challenge in mortgage finance.) So by default this is a lose-lose situation for the lender: if rates rise the value of the loan falls, if rates fall the loan very possibly gets repaid early. But with the origination fee from the installer, if rates fall and the loan is repaid early, the return on capital over the lifetime of the loan rises sharply.
If the loan is repaid after 7 years, which is approximately the average tenure in a house in the U.S., the real rate is about 8.15%. If it’s extinguished after a year, perhaps due to rates-related refinancing, about 12%.
These numbers start to sound attractive to credit funds, particularly when you have a repeatable process for generating them at 9 figure scales with independent credit quality.
As an additional wrinkle: is Sunlight the ultimate source of capital at risk? Well, if I were Sunlight, I might think of tapping the booming private credit market: borrow at a lower rate than I earn in expectation on my portfolio, collect the spread. If I were Apollo (such a natural brand to associate with sunlight, and among the world’s largest credit funds), I might buy an insurer or figure out how to get retail investors private credit exposure to fund billions of dollars to anyone who creates a loan origination engine with demonstrable credit quality.
For much more on that side of things, you should read Money Stuff or listen to Odd Lots, which cover “private credit is the new bank lending” all the time. I’m just presenting the speculative case for how private credit turns permanent capital vehicles into windows.
Compliance will tell you not to describe this as unsecured lending to the customer. I am so forgetful as to offhand comments made during sales presentations, though.
Formally, the lender does have a security interest. However, they do not want to go to the trouble of “dirtying the title” by getting a lien on the house. That can’t be done in 15 minutes. No, they only have a security interest in the window they financed.
A security interest in a car is valuable because people are quite attached to their cars and, if push comes to shove, you can repossess a car. A security interest in a house is valuable because people are quite attached to their homes and, if push comes to shove, you can foreclose on a mortgage and repossess the home. A security interest in a window is valuable because… a security interest in a window is actually not valuable.
However, by construction, the commanding majority of borrowers here have excellent credit. One factor decreasing their credit risk is that many consumers are, and this is an underwriting term of art, “judgement proof.” If you sue them for performance and a court gives you a judgement, that is worth the paper it is printed on, because they have no easily attachable assets and they might have employment in a System D fashion where garnishing their income is difficult.
A homeowner, on the other hand, always has one asset you can attach: the house, by filing a lien on it after receiving the judgement. A lien against a house is an immediately monetizable asset in the United States, because it blocks the sale of the house until it is satisfied, and there is a specialized financial ecosystem which is happy to buy that lien and then attempt collection by some combination of a) asking nicely and then in the alternative b) waiting patiently.
And so the lender’s contract is, to the extent it is concerned with credit risk, concerned with swiftly demonstrating to a court: valid contract, loan paid for windows, customer isn’t paying, issue us judgement, thank you very much, we’d like to file that judgement as a lien against coincidentally the same house. It’s only fair.
Nice new windows are better than broken ones, and the process of buying them is now painless at an attractive financing cost. They are still expensive, but homes are expensive.
Every time anyone mentions innovation in consumer lending, the same comment is made: isn’t this just the financial crisis all over again? Aren’t we stacking up billions of dollars of low-quality loans with intermediating layers of complex products like CDO-squared? Isn’t this going to blow up?
That’s an understandable point of view. But: there is an actual underwriting process here. We replaced “You write a lie on paper, no one reads it” with a computer program that never gets bored at comparing databases. The borrower is actually reasonably good credit quality, rather than a ninja (“no income, no job”; one of the subprime lending era excesses was writing NINJA loans in quantity).
If the installer successfully leans on the origination machine to lower underwriting standards and let anyone who can fog a window buy one with a smile, then the losses are largely not in the regulated banking sector and backstoppable by taxpayers. They’re mostly to sophisticated investors in credit funds, who are being paid handsomely to take that risk. The system is also self-correcting: early defaults would cause the credit funds to tighten their risk appetites and constrain originations fairly quickly, rather than encouraging refinancing to juice origination numbers, until we were all holding (to quote Margin Call) the biggest bag of odorous excrement ever assembled in the history of capitalism.
Besides, if credit quality keeps you up at night, you should be much more concerned about bog-standard commercial real estate loans.